| Ground | Reference | Owner of the Reference | Title | Semantic Mapping | Basis | Anticipation | Challenged Claims |
|---|
| 1 | 2 | 4 | 5 | 6 | 7 | 8 | 9 | 10 | 11 | 12 | 13 | 14 | 15 | 16 | 17 | 18 | 19 | 20 |
|---|
1
 | 1997 INTERNATIONAL SYMPOSIUM ON LOW POWER ELECTRONICS AND DESIGN, PROCEEDINGS. : 173-177 1997
(Dong, 1997) | University of California, Los Angeles (UCLA) | Low Power Signal Processing Architectures For Network Microsensors | ▪ incoming traffic ≈ measurement system
▪ communication protocol ≈ parallel data
| | | | | | | | | | | | X | | X | | | | | X | | |
2
 | UNATTENDED GROUND SENSOR TECHNOLOGIES AND APPLICATIONS IV. 4743: 327-337 2002
(Merrill, 2002) | Sensoria Corporation | Open Standard Development Platforms For Distributed Sensor Networks | ▪ wireless network ≈ wireless network
▪ transmitting unit, transmitting original data frames ≈ sensor network
▪ wireless channels ≈ data rate
| | | | | | | | | X | | X | | | | X | | X | X | | | X |
3
 | USENIX ASSOCIATION PROCEEDINGS OF THE FIFTH SYMPOSIUM ON OPERATING SYSTEMS DESIGN AND IMPLEMENTATION. : 147-163 2002
(Elson, 2002) | University of California, Los Angeles (UCLA) | Fine-grained Network Time Synchronization Using Reference Broadcasts | ▪ transmitting unit, transmitting original data frames ≈ sensor network
▪ intrusion detection module incoming data frames ≈ explicit time
▪ first receiving, first receiving unit ≈ algorithm t
▪ original data ≈ data fusion
| | | X | | | | | X | | X | X | X | | | X | | | | X | | |
4
 | UNATTENDED GROUND SENSOR TECHNOLOGIES AND APPLICATIONS. 3713: 229-237 1999
(Clare, 1999) | Rockwell Science Center | Self-organizing Distributed Sensor Networks | ▪ wireless communication ≈ wireless communication
▪ transmitting unit, transmitting original data frames ≈ sensor network
▪ transmission channels ≈ end user
| | | X | | | | | | | | X | X | | | X | | | | X | | |
5
 | SENSORS, C31, INFORMATION, AND TRAINING TECHNOLOGIES FOR LAW ENFORCEMENT. 3577: 86-95 1999
(Pottie, 1999) | University of California, Los Angeles (UCLA) | Wireless Integrated Network Sensors: Towards Low Cost And Robust Self-organizing Security Networks | ▪ wireless communication ≈ wireless communication
▪ step d ≈ formation process
| | | X | | | | | | | | X | | | | | | | | | | |
6
 | 1998 INTERNATIONAL SYMPOSIUM ON LOW POWER ELECTRONICS AND DESIGN - PROCEEDINGS. : 11-15 1998
(Lin, 1998) | University of California, Los Angeles (UCLA) | CMOS Front End Components For Micropower RF Wireless Systems | ▪ wireless interface ≈ wireless interface
▪ incoming data frames, second receiving unit ≈ power dissipation
▪ data frames ≈ low power level
▪ original data, original data frames ≈ Design method
▪ step b, step d ≈ including a
| | | X | | X | X | X | X | X | X | X | X | | | | | | X | X | | |
7
 | ISCAS 97 - PROCEEDINGS OF 1997 IEEE INTERNATIONAL SYMPOSIUM ON CIRCUITS AND SYSTEMS, VOLS I - IV. : 2817-2820 1997
(Asada, 1997) | University of California, Los Angeles (UCLA) | Low Power Wireless Communication And Signal Processing Circuits For Distributed Microsensors | ▪ incoming data, incoming traffic ≈ recent advances
▪ transmitting unit, transmitting original data frames ≈ sensor network
| | | X | | | | | | X | X | X | X | | | X | | | X | X | | |
8
 | UNATTENDED GROUND SENSOR TECHNOLOGIES AND APPLICATIONS. 3713: 257-268 1999
(Agre, 1999) | Rockwell Science Center | Development Platform For Self-organizing Wireless Sensor Networks | ▪ wireless communication ≈ wireless communication
▪ wireless interface ≈ development platform
▪ transmitting unit, transmitting original data frames ≈ sensor network
▪ transmission channels ≈ end user
| | | X | | | | | | | | X | X | | | X | | | X | X | | |
9
 | WIRELESS NETWORKS. 9 (5): 545-556 SEP 2003
(Zhang, 2003) | HRL Laboratories, LLC (formerly Hughes Research Laboratories), Georgia Institute of Technology | Intrusion Detection Techniques For Mobile Wireless Networks | ▪ intrusion attack ≈ intrusion detection
▪ incoming data frames ≈ wireless networks
| | | X | | | | | | X | X | X | X | X | | | | | X | X | X | |
10
 | COMPUTER COMMUNICATIONS. 25 (15): 1356-1365 SEP 15 2002
(Verwoerd, 2002) | University of Canterbury (UC). Christchurch, New Zealand | Intrusion Detection Techniques And Approaches | ▪ step b, step d ≈ including a
▪ wireless channels ≈ Such method
| | | | | | | | | X | | | | | | | | | | | | |
11
 | IEEE WIRELESS COMMUNICATIONS. 9 (6): 44-51 DEC 2002
(Arbaugh, 2002) | University of Maryland, Hewlett Packard Labs | Your 802.11 Wireless Network Has No Clothes | ▪ incoming data frames ≈ wireless networks
▪ wireless network technology ≈ access points
▪ transmission channels ≈ end user
| | | X | | | | | | X | X | X | X | | | | | X | X | X | | X |
12
 | LCN 2001: 26TH ANNUAL IEEE CONFERENCE ON LOCAL COMPUTER NETWORKS, PROCEEDINGS. : 454-463 2001
(Schmid, 2001) | Lancaster University | An Access Control Architecture For Microcellular Wireless IPv6 Networks | ▪ impersonation detection system, impersonation detection signal ≈ access control mechanism, dependent manner
▪ incoming data frames ≈ wireless networks
| | | X | | | | | | X | X | X | X | X | X | X | X | X | X | X | X | X |
13
 | US20030041244A1
(Levente Buttyan, 2003) | (Original Assignee) Swisscom Mobile AG
(Current Assignee)
Bin 2020 Series 550 Of Allied Security Trust I
| Method for securing communications between a terminal and an additional user equipment | ▪ step a, step b ≈ following steps, including a
▪ data processing unit ≈ short distance
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b)
▪ 35 U.S.C. 102(e) | ▪ teaches secured communications channels over the telecommunications network in paragraph…
▪ discloses a query from the network operator to the user in which said query is intended to be a form of ensuring the…
▪ discloses computers as above but does not discuss the recited security techniques…
▪ teaches that the following security improvements were known techniques and a person of ordinary skill in the art would… | | | | | | | | | | X | | | | | | | X | | |
14
 | US20030217289A1
(Ken Ammon, 2003) | (Original Assignee) Network Security Technologies Inc
(Current Assignee)
Ozmo Licensing LLC
| Method and system for wireless intrusion detection | ▪ wireless communication ≈ wireless communication
▪ communication protocol ≈ communications medium
▪ intrusion attack ≈ intrusion detection
▪ incoming data frames ≈ wireless networks
▪ second receiving unit ≈ authorized device
▪ air interface ≈ different means
▪ wireless network technology ≈ access points
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b) | ▪ teaches the packet inspection system is a border gateway router centralized security manager connected to a plurality…
▪ teaches said applying a credit scoring rule step comprises calculating an internal credit scoring prior to calculating…
▪ discloses a method for providing security to computer communications whereby increased measures are invoked when a user…
▪ discloses wherein the event parameters include one or more of… | X | | | | | | X | X | X | X | X | X | | | X | X | X | X | X |
15
 | US20020150228A1
(Narumi Umeda, 2002) | (Original Assignee) NTT Docomo Inc
(Current Assignee)
NTT Docomo Inc
| Mobile communication system, resource switching method thereof, network control apparatus included therein, same and network control method | ▪ wireless communication ≈ wireless communication
▪ transmitting unit ≈ receiving means
▪ step d ≈ said method
| ▪ 35 U.S.C. 103(a) | ▪ teaches notifying of the electromagnetic wave environment measurement result of detection to report to central network… | X | | | | | | | | X | | | | X | | | | | | |
16
 | US20030110394A1
(Clifford Sharp, 2003) | (Original Assignee) Deep Nines Inc
(Current Assignee)
Trend Micro Inc
| System and method for detecting and eliminating IP spoofing in a data transmission network | ▪ original data frames, data frames ≈ temporary storing, flow rate
▪ time interval ≈ temporarily store
▪ data processing unit ≈ temporary storage
▪ incoming traffic ≈ flow control, data packet
▪ step d ≈ comprises a, said method
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ teaches the motivation for separating charges based on use in order to balance the total margin for a user s…
▪ teaches the database of sequence is a database of a fixed size such that when the database of sequence is filled to…
▪ teaches carrier may add or offset a subscribers bill based on service level agreement which makes obvious that…
▪ teaches blocking the detected malicious packet comprises instructing a firewall to reject the detected malicious… | X | | X | X | X | X | X | X | X | X | | | | | | X | X | | |
17
 | US20020176378A1
(Thomas Hamilton, 2002) | (Original Assignee) AVIAN COMMUNICATIONS; Proquent Systems Corp
(Current Assignee)
Bytemobile Network Services Corp
| Platform and method for providing wireless data services | ▪ communication protocol ≈ Internet Protocol
▪ wireless network ≈ wireless network
▪ time interval ≈ time interval
▪ incoming traffic ≈ data packet
▪ wireless channels ≈ data rate
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses multiple policies for a specific user indexed by different aliases…
▪ discloses a system further comprising a fourth interface module for interacting with a third party system…
▪ discloses wherein the relevant session information is at least one among an IP address…
▪ discloses the second device can automatically set the first device in the suspend state and set the active state of the… | | | | | X | | X | | | X | | X | | | X | X | X | | X |
18
 | US20020032774A1
(Edward Kohler, 2002) | (Original Assignee) Mazu Networks Inc
(Current Assignee)
Riverbed Technology Inc
| Thwarting source address spoofing-based denial of service attacks | ▪ second receiving, second receiving unit ≈ source addresses
▪ incoming traffic ≈ take action
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ teaches a system comprising sending a event message to a network management station paragraph…
▪ discloses tracking the amount of ingoing to outgoing traffic for each source to determine an attack column…
▪ teaches dropping packets in particular providing a discarded packet count in the analogous art of discarding packets…
▪ teaches the invention substantially as claimed and described in claim… | | | | | | | | | | X | | | | | | | X | | |
19
 | US20020131366A1
(Clifford Sharp, 2002) | (Original Assignee) Deep Nines Inc
(Current Assignee)
Trend Micro Inc
| System and method for traffic management control in a data transmission network | ▪ original data frames, data frames ≈ temporary storing, flow rate
▪ time interval ≈ temporarily store
▪ data processing unit ≈ temporary storage
▪ incoming traffic ≈ flow control, data packet
▪ step b, step d ≈ including a, comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ teaches that information associated with billing includes information with respect to usage service agreement terms…
▪ discloses wherein the digital rights information is a pointer to link a user to a property rights database…
▪ teaches a method a gateway system and a computer program product embodied on a computer readable medium for detecting…
▪ teaches an intelligent feedback loop process that increases a scanning rate responsive to a generation of an event… | X | | X | X | X | X | X | X | X | X | | | | | | X | X | | |
20
 | JPH1146196A
(Takayuki Nakanishi, 1999) | (Original Assignee) Fujitsu Ltd; 富士通株式会社 | Communication device, communication terminal, and program recording medium | ▪ original data frames ≈ 記憶手段と
▪ impersonation detection system, data processing unit ≈ apparatus
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ discloses all of the subject matter as discussed in the rejection of claim…
▪ discloses wherein arbitrary performance of sending the payload payment data digital payload data and incentive payment…
▪ teaches information gathered externally from multiple sources including proxy information and data mining internet…
▪ discloses processing video content and audio content so that all users will be able to view the video… | X | | | | | X | | X | X | X | X | X | X | X | X | | X | X | X |
21
 | US6198728B1
(Samir N. Hulyalkar, 2001) | (Original Assignee) Philips North America LLC
(Current Assignee)
Uniloc 2017 LLC
| Medium access control (MAC) protocol for wireless ATM | ▪ wireless communication ≈ wireless communication
▪ communication protocol ≈ communications medium, first packet
▪ step d ≈ transmitting packets, comprises a
▪ incoming traffic ≈ data packet
▪ step a ≈ node b
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ teaches a wireless communication network as recited in claim…
▪ teaches a method of making use of the acknowledgement to determine the uplink transmission activity…
▪ teaches delaying a random period of time prior to sending the information see column…
▪ discloses that it was known in the art at the time of the invention to organize a contiguous group of cells into… | X | | | | | | | | X | X | | X | | | | | X | | |
22
 | US5561689A
(Arthur E. Fleek, 1996) | (Original Assignee) International Business Machines Corp
(Current Assignee)
International Business Machines Corp
| Method and apparatus for digital carrier detection in a wireless lan | ▪ incoming data, first receiving unit ≈ frequency drift, rising edges
▪ step a ≈ first frequency
▪ transmitting unit ≈ receiving means
▪ outgoing data ≈ binary signal
▪ step b ≈ clock pulses
| | | X | | X | X | X | | X | X | X | X | | | X | | | X | X | | |
23
 | US20030187986A1
(Jim Sundqvist, 2003) | (Original Assignee) Operax AB
(Current Assignee)
NetSocket Inc
| Method for, and a topology aware resource manager in an ip-telephony system | ▪ communication protocol ≈ Internet Protocol
▪ step a, step b ≈ following steps
▪ step d ≈ comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ teaches the invention as claimed including the system of claim…
▪ discloses a method of assessing speech quality transmitted via a packet based telecommunications network ie voice over…
▪ discloses substantial features of the claimed invention it fails to explicitly disclose wherein receiving the current…
▪ discloses determining con guration parameters during the discovery process in paragraph… | | | | | | | | | | | | X | | | | | | | |
24
 | US20030185361A1
(Alexander Edwards, 2003) | (Original Assignee) British Telecommunications PLC
(Current Assignee)
British Telecommunications PLC
| Fraud monitoring system | ▪ second receiving unit ≈ comprises information
▪ time interval ≈ current time period
▪ transmitting unit ≈ receiving pattern
▪ step b, step d ≈ including a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b) | ▪ discloses an apparatus and method for identifying a call record that is to be delivered from one automatic call…
▪ discloses enabling the artificial intelligence engine to draw inferences to form a context for forming the answer to the…
▪ discloses wherein said current time interval and said previous time interval are overlapping col…
▪ discloses all the limitations of subject matter with the exception of the following limitation which are disclosed by… | | | | | X | | | | | X | | | X | | | | X | | |
25
 | US20030126468A1
(Thomas Markham, 2003) | (Original Assignee) Secure Computing LLC
(Current Assignee)
McAfee LLC
| Distributed firewall system and method | ▪ intrusion attack ≈ network interface cards
▪ incoming data, incoming data frames ≈ packet transfer
▪ step b, step d ≈ including a, comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses one or more interfaces to one or more communications channels that may include one or more interfaces to user…
▪ discloses wherein the digital rights information is a pointer to link a user to a property rights database…
▪ teaches storing a second record with mapping information in the memory mapped file…
▪ discloses A client session s time stamp is updated each time a message transaction containing the session id for the… | X | | | | | | X | X | X | X | X | | | | | X | X | X | |
26
 | US20030151513A1
(Falk Herrmann, 2003) | (Original Assignee) Robert Bosch GmbH
(Current Assignee)
Robert Bosch GmbH
| Self-organizing hierarchical wireless network for surveillance and control | ▪ second receiving unit ≈ radio module
▪ original data ≈ first layer
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses wherein the determining that at least one mote device is operating outside normal operational parameters and…
▪ teaches that interconnected wireless devices use mesh network…
▪ teaches a system that covers substantially all limitations of the parent claim…
▪ discloses having a linknode failure metric including node mobility with a mean time to failure for a route based on node… | X | | | | | X | | X | X | X | | | | | | | X | | |
27
 | US20030051041A1
(Asawaree Kalavade, 2003) | (Original Assignee) Tatara Systems Inc
(Current Assignee)
Smith Micro Software Inc
| Method and apparatus for integrating billing and authentication functions in local area and wide area wireless data networks | ▪ wireless network ≈ local area networks
▪ wireless network technology ≈ access points
▪ step d ≈ comprises a, said method
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses displaying which route is used for routing the call on a display of the terminal claim…
▪ teaches a wireless interface communicating at a frequency of approximately…
▪ teaches in an analogous art wherein system determines via monitoring using the probe server whether the at least one…
▪ discloses utilizing RADIUS and GPRS environments but does not disclose modifying RADIUS accounting data to generate GPRS… | | | | | | | | | | | | | | | X | X | | | X |
28
 | US20030028808A1
(Noriyuki Kameda, 2003) | (Original Assignee) NEC Corp
(Current Assignee)
NEC Corp
| Network system, authentication method and computer program product for authentication | ▪ original data ≈ authentication method
▪ step d ≈ comprises a
▪ step a ≈ step a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses wherein the digital rights information is a pointer to link a user to a property rights database…
▪ teaches that timestamps can be used as a substitute to random in authentication to prevent replay attacks…
▪ discloses the additional state comprises storing a pair wise master key wherein the pair wise master key is used by the…
▪ teaches storing a second record with mapping information in the memory mapped file… | X | | | | | X | | X | X | | | | | | | | | | |
29
 | US20030217283A1
(Scott Hrastar, 2003) | (Original Assignee) AirDefense Inc
(Current Assignee)
Extreme Networks Inc
| Method and system for encrypted network management and intrusion detection | ▪ intrusion detection module, impersonation detection signal ≈ processing element
▪ wireless network ≈ wireless network
▪ transmitting unit ≈ receiving means
▪ original data ≈ comprises two
▪ time interval ≈ time interval
▪ step d ≈ comprises a
▪ incoming data frames, data processing unit ≈ fixed time
▪ step b ≈ steps c
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses a communication system comprising a first information processing apparatus and a second information processing…
▪ teaches a well known technique to establish a secure communication channel between two entities the hybrid…
▪ teaches the packet inspection system is a border gateway router centralized security manager connected to a plurality…
▪ teaches wherein the network information includes a list of wireless access point devices and associated parameters… | X | X | | | X | X | X | X | X | X | X | | X | X | X | X | X | X | X |
30
 | US20030219008A1
(Scott Hrastar, 2003) | (Original Assignee) AirDefense Inc
(Current Assignee)
Extreme Networks Inc
| System and method for wireless lan dynamic channel change with honeypot trap | ▪ wireless communication network ≈ wireless communication network
▪ intrusion attack ≈ intrusion detection
▪ intrusion detection module, impersonation detection signal ≈ processing element
▪ transmitting unit ≈ receiving means
▪ step d ≈ comprises a
▪ step b ≈ steps c
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ teaches a well known technique to establish a secure communication channel between two entities the hybrid…
▪ discloses a communication system comprising a first information processing apparatus and a second information processing…
▪ teaches wherein when the unatuhrozied access point is detected the network monitor isolates network communication with…
▪ teaches the packet inspection system is a border gateway router centralized security manager connected to a plurality… | X | X | | | | | | | X | X | X | | X | X | | X | X | X | |
31
 | JP2003288282A
(Ichiro Miyajima, 2003) | (Original Assignee) Fujitsu Ltd; 富士通株式会社 | Unauthorized access prevention program | ▪ transmitting unit ≈ receiving step
▪ wireless communication, wireless network ≈ 前記受
▪ impersonation detection system ≈ detecting
▪ intrusion detection module incoming data frames ≈ の対策
▪ step a ≈ step a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b)
▪ 35 U.S.C. 102(e) | ▪ teaches sending signal periodically in a predetermined time interval to perform a network connection status detection…
▪ discloses a permission negotiation engine to negotiate permissions that haven t been approved by the rights holder…
▪ discloses all the subject matter of the method as discussed above with respect to claim…
▪ discloses a payment system coupled on a communication network see… | X | | | | | | | | X | X | X | X | X | X | X | X | | X | X |
32
 | JP2003289337A
(Masaru Katayama, 2003) | (Original Assignee) Nippon Telegr & Teleph Corp <Ntt>; 日本電信電話株式会社 | Communication network, router, and distributed denial of service attack detection and protection method | ▪ incoming data, intrusion detection module incoming data frames ≈ transmission source address, apparatus
▪ transmitting unit ≈ receiving means
▪ wireless communication, wireless network ≈ 前記受
| | | X | | | | | | X | X | X | X | X | X | X | X | X | X | X | X | X |
33
 | US20030186679A1
(David Challener, 2003) | (Original Assignee) International Business Machines Corp
(Current Assignee)
International Business Machines Corp
| Methods, apparatus and program product for monitoring network security | ▪ time interval ≈ regular intervals
▪ step d ≈ comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ teaches a system for detecting unauthorized access points comprising a database of authorized access points paragraph…
▪ discloses wherein the GPS data comprises IP address and geographic coordinates…
▪ teaches wherein upon determining that the message originated from a mobile wireless device associated with an…
▪ teaches a well known technique to establish a secure communication channel between two entities the hybrid… | | | | | X | | | | | | | | | | | | | | |
34
 | US20030188190A1
(Jeffrey Aaron, 2003) | (Original Assignee) BellSouth Intellectual Property Corp
(Current Assignee)
AT&T Delaware Intellectual Property Inc
| System and method of intrusion detection employing broad-scope monitoring | ▪ intrusion attack ≈ intrusion detection
▪ wireless network ≈ wireless network
▪ step d ≈ comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ teaches such a method wherein said outputting further comprises performing a cross site scripting XSS test on said…
▪ discloses inspecting the TCP stream to detect information indicative of a security breach comprises storing a plurality…
▪ discloses using a key lease in a secondary authentication protocol after a primary authentication protocol has been…
▪ discloses an apparatus and method for fraud prevention when accessing through wireless local area networks… | | | | | | | | | | | X | | | | X | X | | X | X |
35
 | JP2003264595A
(Yosuke Kinoshita, 2003) | (Original Assignee) Mitsubishi Electric Corp; 三菱電機株式会社 | Packet relay device, packet relay system, and october guidance system | ▪ original data frames ≈ 汎用データ
▪ communication protocol ≈ セッション
▪ intrusion detection module, intrusion attack ≈ 侵入検知, apparatus
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ teaches the benefit of flexible configuration by using scripts with installation of software on different hardware…
▪ teaches extracting the link information for access to a site on a communication network storing information of a…
▪ teaches an unwanted mail discriminating apparatus comprising mail receiving means for receiving email ie the system…
▪ discloses wherein at least one of the first operating system column… | X | X | | | | X | | X | X | X | X | X | X | X | X | X | X | X | X |
36
 | US20030149891A1
(Brant Thomsen, 2003) | (Original Assignee) 3Com Corp
(Current Assignee)
3Com Corp
| Method and device for providing network security by causing collisions | ▪ intrusion attack ≈ said devices
▪ step d ≈ said method
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ teaches an aggregation classifier which uniquely identifies the tunnel encapsulation the constituent flows that are…
▪ teaches the user requests propagated to all routers along the data path allowing the network to reconfigure a request…
▪ discloses a method for detecting unauthorized attempts to access a wireless data communication system where the method…
▪ teaches all the particulars of the claim except wherein the estimated position of the second wireless access point is… | | | | | | | | | | | X | | | | | | | X | |
37
 | US20020167965A1
(James Beasley, 2002) | (Original Assignee) Strix Systems Inc
(Current Assignee)
Aurix Pte Ltd
| Link context mobility method and system for providing such mobility, such as a system employing short range frequency hopping spread spectrum wireless protocols | ▪ impersonation detection signal ≈ range wireless communication
▪ air interface ≈ communication link
▪ communication protocol ≈ Internet Protocol
▪ wireless network ≈ wireless network
▪ wireless node ≈ network nodes
▪ wireless network technology ≈ access points
▪ step d ≈ comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b)
▪ 35 U.S.C. 102(e) | ▪ discloses mobility management process includes a mobility protocol a mobility management entity and a mobility process…
▪ discloses a method for establishing communication between a client computer and a network remote from the client…
▪ teaches a system for data distribution using peers to act as relays…
▪ teaches the use of the TCPIP protocol for network communications… | X | X | | | | | X | | X | X | | X | X | X | X | X | X | | X |
38
 | US20030105881A1
(Julie Symons, 2003) | (Original Assignee) HP Inc
(Current Assignee)
Hewlett Packard Development Co LP
| Method for detecting and preventing intrusion in a virtually-wired switching fabric | ▪ incoming data, incoming data frames ≈ switching fabric
▪ intrusion attack ≈ said devices
▪ step d ≈ comprises a, said method
▪ second receiving unit ≈ switch port
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ discloses wherein the parental control device issues a third transaction from the parental control device that is…
▪ teaches a system for relaying messages from an external network into an internal network through a gateway…
▪ discloses sending an access denied message to the user device paragraph…
▪ discloses an apparatus for providing network security comprising A layer… | X | | | | | | X | X | X | X | X | | | | | X | X | X | |
39
 | CN1422039A
(谷大武, 2003) | (Original Assignee) 上海交通大学 | 可控计算机网络的分布式黑客追踪系统 | ▪ time interval ≈ 时间间隔
▪ first receiving, second receiving ≈ 的接收
▪ incoming traffic ≈ 的参数
▪ communication protocol ≈ 网络路
▪ transmitting outgoing data frames ≈ 的通信
| | | | | | | X | | | | | X | | X | | | | X | X | | |
40
 | US20030084321A1
(Richard Tarquini, 2003) | (Original Assignee) HP Inc
(Current Assignee)
Hewlett Packard Development Co LP
| Node and mobile device for a mobile telecommunications network providing intrusion detection | ▪ intrusion attack ≈ intrusion detection
▪ incoming traffic ≈ data packet
▪ step d ≈ comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ teaches wherein the network information includes a list of wireless access point devices and associated parameters…
▪ discloses the malware detection and mitigation system of claim…
▪ teaches de ning threshold based upon a percentage of bandwidth capacity of the network paragraph…
▪ discloses a plurality of data bases including mission objective tables vulnerability tables and network con guration… | | | | | | | | | | X | X | | | | | | X | X | |
41
 | US20020057764A1
(Angelo Salvucci, 2002) | (Original Assignee) Angelo Salvucci; Reich Don E.; Warner Kurt E.; Cook William C.
(Current Assignee)
911 Notify Inc
| Real-time incident and response information messaging in a system for the automatic notification that an emergency call has occurred from a wireline or wireless device | ▪ wireless communication network ≈ telecommunications system
▪ step b, step d ≈ including a
▪ incoming traffic ≈ data packet
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ discloses with the recipient notification communication including notification information comprising a help…
▪ discloses the positioning procedure being performed for an emergency call originated by the UE and sending a location…
▪ discloses that determining a language based on said one or more parameters…
▪ discloses the SMLC transmits a location response to the SGSN which is transmitted to the GMLC but fails to explicitly… | X | | | | | | | | X | X | | | | | | | X | | |
42
 | US20030063714A1
(Peggy Stumer, 2003) | (Original Assignee) Siemens Information and Communication Networks Inc
(Current Assignee)
Unify Inc
| Internet protocol (IP) emergency connections (ITEC) telephony | ▪ communication protocol ≈ Internet Protocol
▪ intrusion attack ≈ said devices
▪ incoming data frames ≈ more series
▪ step b, step d ≈ including a, said method
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses the positioning procedure being performed for an emergency call originated by the UE and sending a location…
▪ teaches a system and method that covers substantially all limitations of the parent claim…
▪ discloses the SMLC transmits a location response to the SGSN which is transmitted to the GMLC but fails to explicitly…
▪ discloses wherein if the communication device is not associated with an automatic locating device and if the received IP… | X | | | | | | X | X | X | X | X | X | | | | X | X | X | |
43
 | US20020066034A1
(Barry Schlossberg, 2002) | (Original Assignee) Schlossberg Barry J.; Wenbiao Wang | Distributed network security deception system | ▪ communication protocol ≈ communication protocol
▪ first receiving, first receiving unit ≈ algorithm t
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ teaches one or more agents send collected header information to a master…
▪ teaches wherein identifying a threat assessment system operable to evaluate the identified threat type comprises…
▪ teaches wherein the verified common configuration command is obtained by verifying the authenticity of the common…
▪ describes reporting the time of day of when the suspicious activity took place… | | | | | | | | | | X | | X | | | | | X | | |
44
 | JP2003092605A
(Tsukasa Kimura, 2003) | (Original Assignee) Nippon Telegr & Teleph Corp <Ntt>; 日本電信電話株式会社 | Content protection method and system, content protection program, and storage medium storing content protection program | ▪ wireless network ≈ 該電子メール
▪ original data ≈ 検出手段と
▪ step b, step d ≈ includes a
▪ impersonation detection system, data processing unit ≈ apparatus, detecting
▪ wireless network technology ≈ technique
| | | X | | | | | X | | X | X | X | X | X | X | X | X | X | X | X | X |
45
 | US20020055980A1
(Steve Goddard, 2002) | (Original Assignee) University of Nebraska
(Current Assignee)
University of Nebraska
| Controlled server loading | ▪ wireless communication network ≈ multiple client
▪ step b, step d ≈ including a, comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b)
▪ 35 U.S.C. 102(e) | ▪ teaches a media element library that is able to return the status of robots which includes the availability of robots…
▪ teaches the invention as claimed including a method of coordinating media requests from a plurality of sources that…
▪ discloses wherein the amount of data process is determined by a of back end servers that are available to receive the of…
▪ teaches servicing requests in the queue based at least in part on their assigned normalized priority includes… | X | | | | | | | | X | | | | | | | | | | |
46
 | US20020146002A1
(Takayuki Sato, 2002) | (Original Assignee) Allied Telesis KK
(Current Assignee)
Allied Telesis KK
| Network administration apparatus, network administrating program, network administrating method and computer network system | ▪ time interval ≈ predetermined time period
▪ transmitting unit, transmitting outgoing data frames ≈ receiving device
▪ step d ≈ comprises a, said method
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b) | ▪ discloses a network device and method for use in a network the method comprising receiving or generating a packet or… | | | | | X | | | | | | | | X | | | X | | | |
47
 | US20030056001A1
(Ashutosh Mate, 2003) | (Original Assignee) Nokia Inc
(Current Assignee)
Nokia Technologies Oy
| Selective routing of data flows using a TCAM | ▪ incoming traffic ≈ packet header information
▪ step d ≈ said steps
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ teaches comparisons are performed in parallel in a single clock cycle paragraph…
▪ discloses a stacking configuration for network switches ie aggregate device fig…
▪ discloses the first classification is based upon the destination port associated the packet column…
▪ discloses a memorypointer and memory payload structure for router EPIC… | | | | | | | | | | X | | | | | | | X | | |
48
 | US20020021675A1
(Anja Feldmann, 2002) | (Original Assignee) AT&T Corp
(Current Assignee)
AT&T Corp
| System and method for packet network configuration debugging and database | ▪ communication protocol, wireless network technology ≈ traffic engineering
▪ incoming traffic ≈ network policies
▪ original data, original data frames ≈ order r
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b) | ▪ discloses an apparatus comprising a processor a memory including computer program code configured to with the processor…
▪ discloses the method system computer readable storage medium of claims…
▪ teaches a method and system wherein establishing a secure connection includes establishing a secure connection over an…
▪ teaches triggering an automatic retrieval of a schema definition file based on the receiving of the request message… | X | | | | | X | | X | X | X | | X | | | X | | X | | X |
49
 | US20020083343A1
(Mark Crosbie, 2002) | (Original Assignee) HP Inc
(Current Assignee)
Hewlett Packard Enterprise Development LP
| Computer architecture for an intrusion detection system | ▪ intrusion attack ≈ intrusion detection
▪ wireless channels, wireless network ≈ low bandwidth
▪ original data, second receiving ≈ reading means
▪ outgoing data frames comprises frames ≈ control agent
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b) | ▪ teaches the claimed invention substantially including the method of claims…
▪ discloses a method of database management in which items in which items contained within a database can be automatically…
▪ discloses thresholds as detection criteria while threshold parameters such as of events and the time duration in which…
▪ discloses a system wherein the one or more biometric identi ers include ngerprints retinal scans or images of the… | X | | | X | | X | X | X | X | X | X | | | | X | X | X | X | X |
50
 | EP1160646A2
(Arturo Maria, 2001) | (Original Assignee) AT&T Wireless Services Inc
(Current Assignee)
AT&T Wireless Services Inc
| Floating intrusion detection platforms | ▪ intrusion attack ≈ software agent
▪ step d ≈ said steps
▪ step b ≈ steps c
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses that the system for managing security events includes honeypots…
▪ discloses an alert gateway system that analyze how to communicate alert messages which are communicated to subscribers…
▪ discloses in response receiving a request for con guring a connection checking to see weather request is a malicious…
▪ discloses the second means includes means for adjusting times at which the network messages are sent by the third means… | | | | | | | | | | | X | | | | | | | X | |
51
 | EP1259026A1
(Claude Castelluccia, 2002) | (Original Assignee) Motorola Solutions Inc
(Current Assignee)
Motorola Solutions Inc
| Method and device for managing mobile nodes | ▪ step b, step d ≈ including a
▪ incoming traffic ≈ data packet
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ teaches that it is desirable to check the available bandwidth before allocating a datagram COL…
▪ teaches a dynamic network management system in a communication system including a mobile access router forming a…
▪ teaches tracking IP addresses assigned to a mobile node where the IP addresses are assigned by a of foreign networks…
▪ teaches wherein the base station is stationary and at least one of said plurality of nodes is connected to a vehicle… | | | | | | | | | | X | | | | | | | X | | |
52
 | US20020065938A1
(Peder Jungck, 2002) | (Original Assignee) Cloudshield Tech Inc
(Current Assignee)
LOOKINGGLASS CYBER SOLUTIONS Inc
| Edge adapter architecture apparatus and method | ▪ step d ≈ said method, comprises a
▪ incoming data, incoming data frames ≈ other port
▪ intrusion detection module incoming data frames ≈ one second
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses one or more rules where rules are a functional form of a model see…
▪ discloses capable of analyzing any portion of the packet including the header and payload…
▪ discloses if downstream IP packets were received from the DSL line upstream packets will be routed to a DSL modem in…
▪ teaches identifying a codec associated with the data stream see US… | X | | | | | | X | X | X | X | | X | | | | X | X | | |
53
 | EP1154610A2
(Marc Lamberton, 2001) | (Original Assignee) International Business Machines Corp
(Current Assignee)
International Business Machines Corp
| Methods and system for defeating TCP Syn flooding attacks | ▪ communication protocol ≈ Internet Protocol
▪ step d ≈ said method
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ discloses method and apparatus for rate based denial of service attack detection and prevention comprising the following…
▪ discloses wherein the items included in the first item group are a transmission source address and a destination port…
▪ teaches the motivation of presenting to the users a value with respect to the advertising selected with respect to…
▪ teaches wherein evaluating the feature comprises determining the feature over a predefined of first content bytes at a… | | | | | | | | | | | | X | | | | | | | |
54
 | US20010012296A1
(Jon Burgess, 2001) | (Original Assignee) 3Com Corp
(Current Assignee)
HP Inc
;
Hewlett Packard Enterprise Development LP
| Multi-port network communication device with selective mac address filtering | ▪ step b, step d ≈ including a
▪ incoming traffic ≈ data packet
| | | | | | | | | | | | X | | | | | | | X | | |
55
 | US6580372B1
(Scott C. Harris, 2003) | (Original Assignee) Scott C. Harris | Automatic electronic device detection | ▪ intrusion detection module, impersonation detection signal ≈ processing element
▪ incoming traffic ≈ taking action
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ teaches a method for inhibiting wireless telecommunication system comprising broadcasting a noise signal col…
▪ discloses device enumeration functionality that polls attached hardware devices in pages…
▪ discloses the use of a RF shield copper mesh at a gas station so as to inhibit cellular telephone communications in…
▪ teaches that a broadcasting the plurality of noise signals from different locations into the region such that the… | X | X | | | | | | | X | X | X | | X | X | | X | X | X | |
56
 | US6647418B1
(Arturo Maria, 2003) | (Original Assignee) AT&T Wireless Services Inc
(Current Assignee)
AT&T Mobility II LLC
;
AT&T Wireless Services Inc
| Method and apparatus for filtering packets using a dedicated processor | ▪ wireless network technology ≈ dynamic random access memory
▪ wireless network ≈ wireless network
▪ step d ≈ comprises a
▪ transmission channels ≈ end user
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses one or more interfaces to one or more communications channels that may include one or more interfaces to user…
▪ teaches a distributed computer system including a distributed shared memory see abstract…
▪ discloses wherein the digital rights information is a pointer to link a user to a property rights database…
▪ teaches storing a second record with mapping information in the memory mapped file… | | | | | | | | | | X | | | | | X | X | X | | X |
57
 | US6519703B1
(James B. Joyce, 2003) | (Original Assignee) James B. Joyce
(Current Assignee)
Bandura Cyber Inc
| Methods and apparatus for heuristic firewall | ▪ intrusion detection module, impersonation detection signal ≈ processing element
▪ transmission channels ≈ frequency domain
▪ step d ≈ comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses a method and system for adaptive network security using intelligent packet analysis comprising reassembling a…
▪ teaches de ning threshold based upon a percentage of bandwidth capacity of the network paragraph…
▪ teaches issuing a SNMP trap sending email alert logging the problem…
▪ teaches requesting that a host name be mapped receiving an IP address wherein said host name has been mapped to said… | X | X | | | | | | | X | X | X | | X | X | | X | X | X | |
58
 | US6338082B1
(Eric Schneider, 2002) | (Original Assignee) Eric Schneider
(Current Assignee)
Mec Management LLC
| Method, product, and apparatus for requesting a network resource | ▪ time interval, data processing unit ≈ network bandwidth
▪ step d ≈ said method
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ teaches the invention substantially as claimed including method product and apparatus for requesting a network…
▪ teaches list of user names identification that are allowed agreed to use a content exchange…
▪ discloses a method comprising the candidate domain name is an internationalized domain name represented using at least…
▪ discloses a technology with which a mobile terminal moving in a PMIP domain receives various types of prefixes and… | | | | | X | | | | | X | | | | | | | X | | |
59
 | US6343212B1
(Matthias Weber, 2002) | (Original Assignee) Sony International Europe GmbH
(Current Assignee)
Sony International Europe GmbH
| Outputting a warning signal when approaching a protected area warning of an impending mode change | ▪ wireless communication ≈ wireless communication
▪ transmitting unit ≈ receiving means
▪ step b, step d ≈ including a
▪ data frames ≈ time period
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b) | ▪ discloses device enumeration functionality that polls attached hardware devices in pages…
▪ discloses a method for transmitting a character message from a mobile communication terminal with a character message…
▪ teaches querying for a parental control associated with the location O…
▪ teaches a control system via system formed by a writeread station and a transponder comprising a control device via… | X | | X | X | X | X | X | X | X | X | | | X | | | X | X | | |
60
 | US6362736B1
(Narayan L. Gehlot, 2002) | (Original Assignee) Nokia of America Corp
(Current Assignee)
SOUND VIEW INNOVATIONS LLC
;
Alcatel Lucent SAS
| Method and apparatus for automatic recovery of a stolen object | ▪ step a ≈ telecommunication device
▪ wireless communication ≈ wireless communication
▪ wireless interface ≈ wireless interface
| ▪ 35 U.S.C. 103(a) | ▪ discloses said monitoring device including a radio transmitter for transmitting radio location signals…
▪ discloses an apparatus for automatic recovery of a stolen object comprising…
▪ discloses the vehicle sensor is a shock sensor motion sensor ignition sensor door sensor or a combination thereof see… | X | | | | | | | | X | | | | | | | X | | | |
61
 | US6149353A
(Byard G. Nilsson, 2000) | (Original Assignee) KUYPER REENA (ONE-EIGHTH INTEREST)
(Current Assignee)
Dot 23 Technologies LLC
| Wireless prepaid telephone system with dispensable intruments | ▪ wireless communication ≈ wireless communication
▪ air interface, data processing unit ≈ transfer command
▪ original data, original data frames ≈ unique control
▪ step b, step d ≈ including a, comprises a
▪ first receiving unit ≈ said area
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b) | ▪ teaches wherein marketing information is audibly transmitted to the user over the network col…
▪ teaches a housing wherein the means comprises an integrally formed tab on the body for location of the retaining plate…
▪ discloses the use of a text communication account the combination of HAMILTON and NILSSON does not expressly disclose…
▪ teaches the body having a plurality of apertures in one face for receiving the keys of a keymat mounted on an inner… | X | | | | | X | | X | X | X | | X | | | | X | X | | |
62
 | US6363489B1
(Oded Comay, 2002) | (Original Assignee) Forescout Technologies Inc
(Current Assignee)
Forescout Technologies Inc
| Method for automatic intrusion detection and deflection in a network | ▪ intrusion detection module ≈ intrusion detection module
▪ transmission channels ≈ one packet
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ teaches fraud perpetrated on users online reduce online sales and raise cost for consumers and vendors and that there…
▪ discloses all subject matter of the claimed invention as discussed above with respect to claims…
▪ discloses that a physical address is invalid if it does not match the one or more secure addresses…
▪ teaches a well known technique to establish a secure communication channel between two entities the hybrid… | X | X | | | | | | | X | X | X | | X | X | | X | X | X | |
63
 | US6281790B1
(David E. Kimmel, 2001) | (Original Assignee) Net Talon Security Systems Inc
(Current Assignee)
NetTalon Security Systems Inc
;
Net Talon Security Systems Inc
| Method and apparatus for remotely monitoring a site | ▪ data frames ≈ remote monitoring
▪ wireless network ≈ wireless network
▪ step b, step d ≈ including a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ teaches a system for detecting intrusion using a plurality of sensors see abstract wherein the system may report…
▪ teaches a floor plan display for remotely remotely monitoring a security system using a plurality of tiles see…
▪ teaches a user interface that allows a user to create and render a monitored floor plan using a component of the user…
▪ teaches wherein the color could also just be displayed as an outline ie border see col… | X | | X | X | X | X | X | X | X | X | | | | | X | X | X | | X |
64
 | US20030147518A1
(Nandakishore A. Albal, 2003) | (Original Assignee) Motorola Solutions Inc
(Current Assignee)
Motorola Solutions Inc
| Methods and apparatus to deliver caller identification information | ▪ second receiving ≈ third communication
▪ wireless network technology ≈ remote data
▪ step a ≈ node b
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses the step of converting the received data corresponding to the message code…
▪ teaches setting up a nonassociated telephone call to the recipient telephone from a simulated calling party having the…
▪ discloses the received and stored calling party information each includes at least a portion of a telephone of the…
▪ teaches a method performed by a voice portal comprising receiving a call from a caller where the call includes… | | | | | | | | | | X | | | | | X | | X | | X |
65
 | US6550012B1
(Emilio Villa, 2003) | (Original Assignee) Network Associates Inc
(Current Assignee)
McAfee LLC
| Active firewall system and methodology | ▪ second receiving unit ≈ comprises information
▪ step d ≈ comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses a network security risk management system that evaluates network threat values…
▪ teaches measuring the network traffic and returns the information to the central manager or another apparatus…
▪ teaches that the computer program provides each said party of the one or more parties access only to said documents…
▪ discloses using formulas to calculate potential threats with assigned factors detected from the network… | | | | | | | | | | X | | | | | | | X | | |
66
 | US6553028B1
(Cheng Tang, 2003) | (Original Assignee) Cisco Technology Inc
(Current Assignee)
Cisco Technology Inc
| Method and apparatus for multicast switching using a centralized switching engine | ▪ air interface ≈ acknowledgment message
▪ incoming traffic, incoming data frames ≈ subsequent frame
▪ wireless communication ≈ n group
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ discloses using a HASH operation in order to select one of a plurality of possible paths to forward a packet page…
▪ discloses the MDT default tunnel and MDT data tunnel see rejection of preceding claims…
▪ discloses assignment being performed sequentially where the next available address is selected page…
▪ teaches about the access policy as per specified transfer rate… | X | | | | | | X | X | X | X | | | | | | X | X | | |
67
 | US6393484B1
(Leonardo C. Massarani, 2002) | (Original Assignee) International Business Machines Corp
(Current Assignee)
International Business Machines Corp
| System and method for controlled access to shared-medium public and semi-public internet protocol (IP) networks | ▪ wireless network technology ≈ access points
▪ step b, step d ≈ including a
▪ transmission channels ≈ end user
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses that the database includes MAC addresses of authorized devices see col…
▪ teaches transmitting correction address resolution requests on the computer network to update the client device with…
▪ discloses the invention provides a method and a system for implementing interface redundancy in a computer network so…
▪ teaches the construction of an MPLS tunnel requiring the use of ARP to discover MAC address information of switches in… | | | | | | | | | | X | | | | | X | | X | | X |
68
 | US6338089B1
(Cian M. Quinlan, 2002) | (Original Assignee) Bull HN Information Systems Inc
(Current Assignee)
Bull HN Information Systems Inc
| Method and system for providing session pools for high performance web browser and server communications | ▪ second receiving unit ≈ predetermined value
▪ step a, step b ≈ following steps
| | | | | | | | | | | | X | | | | | | | X | | |
69
 | US6609205B1
(Thomas E. Bernhard, 2003) | (Original Assignee) Cisco Technology Inc
(Current Assignee)
Cisco Technology Inc
| Network intrusion detection signature analysis using decision graphs | ▪ air interface ≈ multiple sessions
▪ incoming data ≈ incoming data
▪ step d ≈ comprises a
▪ step a ≈ node b
| | | X | | | | | | X | X | X | X | | | | | | X | X | | |
70
 | US6651168B1
(I-Lung Kao, 2003) | (Original Assignee) International Business Machines Corp
(Current Assignee)
International Business Machines Corp
| Authentication framework for multiple authentication processes and mechanisms | ▪ original data ≈ authentication method
▪ wireless communication network, wireless network technology ≈ having access
▪ step b, step d ≈ including a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses a system using a quality meter which compares the quality of password to the minimum threshold and if it does…
▪ discloses a person authentication application data processing system according to…
▪ teaches a mechanism for allowing access to said secure data by a host device on which the data storage device is…
▪ teaches the method comprising signing the statement paragraph… | X | | | | | X | | X | X | | | | | | X | | | | X |
71
 | JPH11316677A
(Eric Grosse, 1999) | (Original Assignee) Lucent Technol Inc; ルーセント テクノロジーズ インコーポレイテッド | How to secure a computer network | ▪ incoming traffic ≈ 通信トラフィック
▪ wireless interface ≈ specific use
▪ step b, step d ≈ includes a
▪ impersonation detection system, data processing unit ≈ apparatus
▪ wireless communication ≈ どうか
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b)
▪ 35 U.S.C. 102(e) | ▪ discloses a system that determines whether the attachment is of a type which is in the list of approved attachments…
▪ teaches wherein the network information includes a list of wireless access point devices and associated parameters…
▪ teaches such a method wherein said outputting further comprises performing a…
▪ teaches the scanning means comprise scanning means for scanning the message for predetermined character strings column… | X | | | | | | | | X | X | X | X | X | X | X | X | X | X | X |
72
 | US6343362B1
(Thomas Henry Ptacek, 2002) | (Original Assignee) Networks Associates Inc
(Current Assignee)
McAfee LLC
| System and method providing custom attack simulation language for testing networks | ▪ communication protocol ≈ Internet Protocol
▪ step d ≈ comprises a, said method
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ discloses a network simulation for analyzing attacks against a network…
▪ teaches information gathered externally from multiple sources including proxy information and data mining internet…
▪ discloses the spam determination at then may include comparing the determined or calculated score andor confidence level…
▪ teaches the processing comprises evaluating one or more parameters selected from among the group consisting of URL… | | | | | | | | | | | | X | | | | | | | |
73
 | US6308053B1
(Byard G. Nilsson, 2001) | (Original Assignee) KUYPER REENA (ONE-EIGHTH INTEREST); Thompson Bettina Jean
(Current Assignee)
RPX Corp
;
Thompson Bettina Jean
| Recyclable wireless telephone unit with a secured activation switch | ▪ wireless communication ≈ wireless communication
▪ step b, step d ≈ including a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ teaches wherein marketing information is audibly transmitted to the user over the network col…
▪ teaches a housing wherein the member includes a support for locating and retaining a printed circuit board thereon see…
▪ teaches a housing including a guide on the body to receive and support electronic components mounted on the member see…
▪ discloses the use of a text communication account the combination of HAMILTON and NILSSON does not expressly disclose… | X | | | | | | | | X | | | | | | | | | | |
74
 | US6415321B1
(Robert E. Gleichauf, 2002) | (Original Assignee) Cisco Technology Inc
(Current Assignee)
Cisco Technology Inc
;
Cisco Systems Inc
| Domain mapping method and system | ▪ intrusion attack ≈ intrusion detection
▪ step d ≈ comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ discloses the query execution data structure comprising of plurality object oriented nodes…
▪ discloses substantial features of the invention such as the method of claim…
▪ teaches wherein the packet is a secure socket layer SSL packet column…
▪ discloses the verifying the fieldoperator pairings in the policy and based on rules associated with dynamic link… | | | | | | | | | | | X | | | | | | | X | |
75
 | US6246935B1
(Stephen J. Buckley, 2001) | (Original Assignee) DaimlerChrysler Co LLC
(Current Assignee)
FCA US LLC
| Vehicle instrument panel computer interface and display | ▪ communication protocol ≈ communications medium
▪ step d ≈ comprises a
| | | | | | | | | | | | | | X | | | | | | | |
76
 | US6510236B1
(Michael A. Crane, 2003) | (Original Assignee) International Business Machines Corp
(Current Assignee)
International Business Machines Corp
| Authentication framework for managing authentication requests from multiple authentication devices | ▪ air interface ≈ communication link
▪ original data ≈ coupled thereto
▪ step b, step d ≈ including a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ teaches of extensible authentication protocol EAP see page…
▪ discloses the method would have been realized by one skill in the art as applicable to the apparatus of…
▪ teaches an electronic document storage and rendering method comprising authenticating a user and electronic…
▪ discloses a system of updating a master biometric template US… | X | | | | | X | | X | X | | | | | | | X | | | |
77
 | US6370648B1
(Thanh A. Diep, 2002) | (Original Assignee) Visa International Service Association
(Current Assignee)
Visa International Service Association
| Computer network intrusion detection | ▪ time interval ≈ predetermined time period
▪ intrusion attack ≈ intrusion detection
▪ step a, step b ≈ frequency f, repeating steps
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ discloses the user requesting to continue playback of a movie which includes the rendering state of where the user…
▪ teaches methods of detecting network exploit defined in a signature…
▪ teaches a TLS handshake that it uses digital certificates for authentication…
▪ teaches information gathered externally from multiple sources including proxy information and data mining internet… | | | | | X | | | | | | X | | | | | | | X | |
78
 | US6321338B1
(Phillip A. Porras, 2001) | (Original Assignee) SRI International Inc
(Current Assignee)
SRI International Inc
| Network surveillance | ▪ air interface, data processing unit ≈ transfer command
▪ step d ≈ comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ teaches wherein the network information includes a list of wireless access point devices and associated parameters…
▪ discloses a plurality of data bases including mission objective tables vulnerability tables and network con guration…
▪ discloses the second means includes means for adjusting times at which the network messages are sent by the third means…
▪ teaches nothing more than predictable results to one of ordinary skill in the art KSR… | | | | | | | | | X | X | | | | | | X | X | | |
79
 | US6327570B1
(Dian Stevens, 2001) | (Original Assignee) Dian Stevens
(Current Assignee)
III Holdings 1 LLC
| Personal business service system and method | ▪ incoming data frames ≈ wireless networks
▪ step d ≈ comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ teaches that by crafting the promotion contract around performance goals evidenced by incremental sales volume…
▪ discloses that portable terminals include a wide range of applications including word processing etc col…
▪ teaches of using various search criteria in selecting healthcare providers of interest pg…
▪ teaches a method of obtaining information about a product or service offering having an associated receiver responsive… | X | | | | | | X | X | X | X | | | | | | X | X | | |
80
 | US6324650B1
(John W.L. Ogilvie, 2001) | (Original Assignee) John W.L. Ogilvie
(Current Assignee)
Resource Consortium Ltd
| Message content protection and conditional disclosure | ▪ air interface ≈ presents data
▪ step b ≈ method steps, steps c
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ discloses or renders obvious the aforementioned further limitation…
▪ discloses the limitation by teaching the encoding property is related to compression paragraphs…
▪ teaches the claimed storing a data encryption flag to indicate that data encryption has been performed…
▪ teaches changing the annotation as similarly explained in the rejection for claim… | | | | | | | | | X | | | | | | | X | | | |
81
 | WO9917477A2
(Jeffrey J. Kriz, 1999) | (Original Assignee) Honeywell Inc. | Multi tier wireless communication system | ▪ wireless communication ≈ wireless communication
▪ incoming data, incoming data frames ≈ relatively high power, logic circuitry
▪ step b ≈ higher power level
▪ transmitting unit, transmitting outgoing data frames ≈ receiving device
▪ wireless channels, wireless network ≈ low bandwidth
▪ transmission channels ≈ video camera
▪ step d ≈ comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses a fuel pump with wireless communication as discussed above…
▪ teaches using the system at a gas station which are old and well known to often be service stations that perform…
▪ teaches an interface device that receives data from a combination of several sources via several different method of…
▪ discloses wherein said interrogator employs antennas selected from the group consisting of far field antennas near field… | X | | | | | | X | X | X | X | | | X | | X | X | X | | X |
82
 | US6195547B1
(Michel Corriveau, 2001) | (Original Assignee) Telefonaktiebolaget LM Ericsson AB
(Current Assignee)
Optis Wireless Technology LLC
| System and method for a previously activated mobile station to challenge network mobile station knowledge during over the air activation | ▪ time interval ≈ programming information
▪ wireless communication ≈ wireless communication
▪ wireless network ≈ wireless network
▪ step b, step d ≈ including a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ discloses the short range wireless link between the portable mobile communications device and the computermedia network…
▪ teaches all the particulars of the claim except the method of claim…
▪ discloses transmitting the request to an operator network and said receiving means is adapted to receive the valid…
▪ discloses a power personal care appliance an electronic toothbrush see fig… | X | | | | X | | | | X | | | | | | X | X | | | X |
83
 | US6317831B1
(Peter F. King, 2001) | (Original Assignee) Great Elm Capital Group Inc
(Current Assignee)
Unwired Planet LLC
| Method and apparatus for establishing a secure connection over a one-way data path | ▪ wireless communication ≈ wireless communication
▪ time interval ≈ temporarily store
▪ outgoing data ≈ outgoing message
▪ step d ≈ said method
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b) | ▪ teaches secured communications channels over the telecommunications network in paragraph…
▪ discloses computers as above but does not discuss the recited security techniques…
▪ teaches that the following security improvements were known techniques and a person of ordinary skill in the art would…
▪ teaches that transmitting the setting information which includes a predetermined private key eg WEP key WPA key or any… | X | | X | X | X | | | | X | | | | | | | X | X | | |
84
 | US6219786B1
(Mark Cunningham, 2001) | (Original Assignee) SurfControl Inc
(Current Assignee)
Forcepoint LLC
| Method and system for monitoring and controlling network access | ▪ intrusion attack ≈ intrusion detection
▪ step b, step d ≈ including a, said method
▪ step a ≈ node b
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ teaches that the computer program provides each said party of the one or more parties access only to said documents…
▪ teaches wherein the network elements comprise data defining hosts associated with the packet flows data defining peers…
▪ teaches a system for managing documents at an electronic data repository wherein the documents relate to a transaction…
▪ discloses the information processing apparatus wherein said operation permissiondenial information generating part… | | | | | | | | | | | X | | | | | | | X | |
85
 | US6519646B1
(Amit Gupta, 2003) | (Original Assignee) Sun Microsystems Inc
(Current Assignee)
Oracle America Inc
| Method and apparatus for encoding content characteristics | ▪ communication protocol ≈ transmitting one
▪ step d ≈ comprises a, said method
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b)
▪ 35 U.S.C. 102(e) | ▪ teaches a method for delivering art information by use of a telecommunication path according to claim…
▪ discloses an electronic shopping method as set forth in claim…
▪ teaches marking each of the plurality of client records that include a logical identification that matches the…
▪ teaches further comprising when a matching client record is not identified in the query marking each of the plurality… | | | | | | | | | | | | X | | | | | | | |
86
 | US6208247B1
(Jonathan R. Agre, 2001) | (Original Assignee) Rockwell Science Center LLC
(Current Assignee)
Skyworks Solutions Inc
| Wireless integrated sensor network using multiple relayed communications | ▪ step b ≈ higher power level
▪ data frames, original data frames ≈ second station, data buffer
▪ first receiving, first receiving unit ≈ first station
▪ time interval ≈ time interval
▪ step d ≈ comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ teaches sensor readings are of environmental conditions selected from a group consisting of temperature humidity…
▪ discloses transmitted to an intended recipient participant by way of one or more intermediating participants and further…
▪ discloses a land based seismic data collection unit abstract…
▪ teaches that the ability to perform the administration remotely greatly supports efficient resource time para… | X | | X | X | X | X | X | X | X | X | | | | | | X | X | | |
87
 | US6256314B1
(Benny Rodrig, 2001) | (Original Assignee) Avaya Technology LLC
(Current Assignee)
Avaya Inc
| Apparatus and methods for routerless layer 3 forwarding in a network | ▪ second receiving unit ≈ comprises information
▪ communication protocol, incoming data ≈ downstream port, upstream port
▪ incoming traffic ≈ data packet
▪ step d ≈ comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ discloses if the received packet is determined to be associated with the packet flow querying at least one database…
▪ discloses a method for performing flow compilation packet processing the method comprising receiving a packet at a…
▪ teaches an operation code for identifying whether a packet is suitable for a particular network interface function by…
▪ teaches wherein at least one of the multiple virtual subrings carries multiple virtual local area networks VLANs para… | X | | | | | | X | X | X | X | | X | | | | X | X | | |
88
 | US6185491B1
(Jamison Gray, 2001) | (Original Assignee) Sun Microsystems Inc
(Current Assignee)
Oracle America Inc
| Networked vehicle controlling attached devices using JavaBeans™ | ▪ wireless channels, transmission channels ≈ digital multimedia broadcasting, video camera
▪ communication protocol ≈ communications medium, internet connection
▪ step b, step d ≈ including a
| | | | | | | | | X | | | X | | X | | | | | X | | |
89
 | US20030043763A1
(Paul D Grayson, 2003) | (Original Assignee) US Philips Corp
(Current Assignee)
Signify Holding BV
| Wireless networked message routing | ▪ intrusion detection module incoming data frames ≈ acknowledgement message
▪ wireless communication ≈ wireless communication
▪ first receiving unit ≈ node address
▪ incoming traffic ≈ data packet
▪ step d ≈ comprises a
▪ step a ≈ node b
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ discloses that the application and the discovery unit are separated not colocated…
▪ teaches that each node has functions of a base transceiver station relay function and a wireless terminal FIG…
▪ teaches that the originate node broadcasts a packet to a plurality of nodes col…
▪ teaches a signal relaying method in a communication system comprising the steps of… | X | | | | | | | | X | X | | | | | | | X | | |
90
 | US6202081B1
(Stanley T. Naudus, 2001) | (Original Assignee) 3Com Corp
(Current Assignee)
HP Inc
;
Hewlett Packard Enterprise Development LP
| Method and protocol for synchronized transfer-window based firewall traversal | ▪ air interface ≈ acknowledgment message
▪ communication protocol ≈ Internet Protocol
▪ step a, step b ≈ following steps
| | | | | | | | | | | X | | | X | | | | X | | | |
91
 | US6363056B1
(Mandis Sadr Mohammad Beigi, 2002) | (Original Assignee) International Business Machines Corp
(Current Assignee)
International Business Machines Corp
| Low overhead continuous monitoring of network performance | ▪ incoming data frames ≈ particular egress
▪ time interval, data processing unit ≈ network bandwidth, time interval
▪ original data, transmission channels ≈ next data packet
▪ wireless network technology ≈ access points
▪ step b ≈ method steps, steps c
▪ communication protocol ≈ first packet
▪ step d ≈ said method
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ teaches providing plural egresses at the source connected to plural network access providers column…
▪ discloses generating the policy using the set of policy data see…
▪ discloses that a third party service level manager SLM may be utilized in order to assist a user in monitoring the…
▪ discloses disclose wherein the computing step includes calculating an accessibility loss due to ingress router failure a… | X | | | | X | X | X | X | X | X | | X | | | X | X | X | | X |
92
 | US6279113B1
(Vimal Vaidya, 2001) | (Original Assignee) Internet Tools Inc
(Current Assignee)
CA Inc
| Dynamic signature inspection-based network intrusion detection | ▪ intrusion attack ≈ intrusion detection
▪ time interval ≈ time interval
▪ step b, step d ≈ including a, said steps
| | | | | | | X | | | | | | X | | | | | | | X | |
93
 | US6557037B1
(Joseph E. Provino, 2003) | (Original Assignee) Sun Microsystems Inc
(Current Assignee)
Oracle America Inc
| System and method for easing communications between devices connected respectively to public networks such as the internet and to private networks by facilitating resolution of human-readable addresses | ▪ communication protocol ≈ response message
▪ step b, step d ≈ including a
▪ wireless network technology ≈ one device
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses setting an error correction code in the tunneling header to re ect modi cations made to convert the initial…
▪ teaches recording an address of said proxy server for said computing system if said computing system is not publicly…
▪ teaches formatting a client s request in accordance with a protocol of the wide area network to produce a formatted…
▪ teaches the method of transferring data between different types of terminals according to claim… | | | | | | | | | | | | X | | | X | | | | X |
94
 | US6275942B1
(Thomas Bernhard, 2001) | (Original Assignee) Network Associates Inc
(Current Assignee)
Networks Associates Technology Inc
;
McAfee LLC
| System, method and computer program product for automatic response to computer system misuse using active response modules | ▪ intrusion detection module, impersonation detection signal ≈ processing element
▪ step a, step d ≈ frequency f
| ▪ 35 U.S.C. 103(a) | ▪ teaches the data signature being passwd in a context where filenames are likely to appear…
▪ discloses the limitation of receiving noti cation of a network intrusion see column… | X | X | | | | | | | X | X | X | | X | X | | X | X | X | |
95
 | US5982281A
(Hoyt M. Layson, 1999) | (Original Assignee) Pro Tech Monitoring Inc
(Current Assignee)
3M Attenti Ltd
| Offender and victim collision avoidance and advanced warning system | ▪ wireless communication, wireless node ≈ wireless communication, digital wireless
▪ data processing unit ≈ Global Positioning
▪ original data ≈ data fusion
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b)
▪ 35 U.S.C. 102(e) | ▪ discloses the use of the barcode scanner to verify that the appropriate medicationdoctors orders eg dosage accuracy are…
▪ discloses a method for providing indications of the state of a…
▪ discloses the plurality of objects is cards or cellular telephones or personal digital assistants PDAs or mobile radio…
▪ teaches a system including a portable monitor including a barcode scanner and also discloses the use of patient… | X | X | | | | X | X | X | X | X | | | X | X | | X | X | | |
96
 | US6167052A
(Thomas G. McNeill, 2000) | (Original Assignee) VPNX com Inc
(Current Assignee)
INTERNAP Corp
| Establishing connectivity in networks | ▪ first receiving ≈ computer instructions
▪ step d ≈ comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b) | ▪ discloses a communication network comprising at least two switches each having a database to hold VLAN membership the…
▪ teaches defining a plurality of default virtual networks based on a plurality of protocols…
▪ discloses system and method for efficiently handling multicast packets by aggregating VLAN context…
▪ discloses interfacing the switch with the virtual router such that the switched network can be provided with access to… | | | | | | | | | | X | | | | | | | X | | |
97
 | US6226751B1
(Leslie J. Arrow, 2001) | (Original Assignee) VPNet Technologies Inc
(Current Assignee)
Avaya Inc
;
VPNet Technologies Inc
| Method and apparatus for configuring a virtual private network | ▪ communication protocol ≈ Internet Protocol
▪ step d ≈ comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses having a VPN unit virtual private network unit enhancement cluster with a compressiondecompression unit…
▪ teaches to use the technique regardless of the current version of IP protocol col…
▪ teaches of a decision box which determines if the source and destination address are both members of the same VPN…
▪ teaches that if the packets are not authenticated they are filtered out wherein an… | | | | | | | | | | | | X | | | | | | | |
98
 | US6246687B1
(Kai-Yeung S. Siu, 2001) | (Original Assignee) Massachusetts Institute of Technology
(Current Assignee)
Massachusetts Institute of Technology
| Network switching system supporting guaranteed data rates | ▪ communication protocol ≈ transferring data
▪ incoming data, incoming data frames ≈ round robin
▪ time interval ≈ FIFO buffer
▪ step d ≈ comprises a
▪ step a ≈ one queue
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b)
▪ 35 U.S.C. 102(e) | ▪ discloses the controller maintain a circuit switch resource table as described above in claims…
▪ discloses that the communications network includes a communications medium PER LINK and wherein the communications…
▪ discloses allocating buffer space to a queue where the buffer space is implemented by assigning a counter limit which…
▪ discloses generating an optimized mapping as a function of the service node relationships and server node relationships… | X | | | | X | | X | X | X | X | | X | | | | X | X | | |
99
 | US6182226B1
(Irving Reid, 2001) | (Original Assignee) Secure Computing LLC
(Current Assignee)
McAfee LLC
| System and method for controlling interactions between networks | ▪ communication protocol ≈ transferring data
▪ step b, step d ≈ including a, comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses a networked personal contact manager title comprising address books for multiple users where users can link to…
▪ discloses a system for managing information sets ie data items at a database ie electronic repository with respect to…
▪ teaches displaying an email address as a unique string col…
▪ teaches that the computer program provides each said party of the one or more parties access only to said documents… | | | | | | | | | | | | X | | | | | | | |
100
 | US6321336B1
(John Applegate, 2001) | (Original Assignee) Secure Computing LLC
(Current Assignee)
McAfee LLC
| System and method for redirecting network traffic to provide secure communication | ▪ intrusion detection module incoming data frames ≈ external network
▪ step b, step d ≈ including a, steps c
| | | X | | | | | | | | | | | | | | | | | | |
101
 | US6263444B1
(Naoyuki Fujita, 2001) | (Original Assignee) National Aerospace Laboratory of Japan; Japan Science and Technology Corp
(Current Assignee)
Japan Science and Technology Agency
;
Japan Aerospace Exploration Agency
| Network unauthorized access analysis method, network unauthorized access analysis apparatus utilizing the method, and computer-readable recording medium having network unauthorized access analysis program recorded thereon | ▪ communication protocol ≈ readable recording medium
▪ original data frames ≈ controlling section
▪ time interval ≈ filtering process
▪ step b ≈ step b
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses the process of enabling the user andor administrator to con gure the event generating module to start…
▪ discloses maintaining a frequency for the of occurances with which messages were rejected…
▪ teaches a method and apparatus for an integrative model of multiple asset classes…
▪ discloses ltering packets using rules based on port and IP address… | X | | | | X | X | | X | X | | | X | | | | | | | |
102
 | US6353614B1
(Michael S. Borella, 2002) | (Original Assignee) 3Com Corp
(Current Assignee)
HP Inc
;
Hewlett Packard Development Co LP
| Method and protocol for distributed network address translation | ▪ communication protocol ≈ response message
▪ step a, step b ≈ following steps, including a
▪ original data ≈ first layer
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ teaches a method of polling network devices for unused IP addresses and releasing IP addresses back to a DHCP server…
▪ discloses routable network address configured to be routed outside a subnet associated with a routable network address…
▪ discloses the use of a user interface to access network related information informing the user of a network connection…
▪ teaches a method wherein the independent networks include the… | X | | | | | X | | X | X | | | X | | | | | | | |
103
 | US6178505B1
(David S. Schneider, 2001) | (Original Assignee) Internet Dynamics Inc
(Current Assignee)
Dropbox Inc
| Secure delivery of information in a network | ▪ step b, step d ≈ including a
▪ air interface ≈ more link
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ teaches that the computer program provides each said party of the one or more parties access only to said documents…
▪ teaches wherein the terminal station includes a central processing unit and a smart card that is in communication with…
▪ discloses a plurality of security service pathways including a combination of rewall and application lleting but doesn t…
▪ teaches a system for managing documents at an electronic data repository wherein the documents relate to a transaction… | | | | | | | | | X | | | | | | | X | | | |
104
 | US6252883B1
(Russell L. Schweickart, 2001) | (Original Assignee) ALOHA Networks Inc
(Current Assignee)
SUMMIT WIRELESS LLC
;
ALOHA Networks Inc
| Home and personal data services overlay communications system | ▪ communication protocol ≈ packet transmission
▪ air interface ≈ communication link
▪ wireless network technology ≈ transmitted data
▪ step a ≈ spreading code
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b) | ▪ teaches of a personal communication device which is able to receive personal data of a user and wherein the personal…
▪ teaches wherein the data from the energy supply and delivery system and the data from the one or more building…
▪ teaches wherein the at least one personal parameter receiver is contained in the wirelessportable…
▪ teaches a method and computer readable medium that provides instruction when executed on a processor for integrating… | | | | | | | | | X | | | X | | | X | X | | | X |
105
 | US6205551B1
(Eric Grosse, 2001) | (Original Assignee) Nokia of America Corp
(Current Assignee)
Nokia of America Corp
;
Provenance Asset Group LLC
;
Nokia USA Inc
| Computer security using virus probing | ▪ step b, step d ≈ including a, comprises a
▪ transmission channels ≈ one packet
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b)
▪ 35 U.S.C. 102(e) | ▪ discloses a system that determines whether the attachment is of a type which is in the list of approved attachments…
▪ teaches wherein the network information includes a list of wireless access point devices and associated parameters…
▪ teaches such a method wherein said outputting further comprises performing a…
▪ teaches the scanning means comprise scanning means for scanning the message for predetermined character strings column… | | | | | | | | | | X | | | | | | | X | | |
106
 | WO9833340A2
(Umesh J. Amin, 1998) | (Original Assignee) At & T Wireless Services, Inc. | Detection of fraudulently registered mobile phones | ▪ wireless network ≈ wireless network
▪ data frames ≈ time period
▪ step d ≈ comprises a
| | | X | | X | X | X | X | X | X | X | X | | | | | X | X | X | | X |
107
 | US6230002B1
(Anders Flodén, 2001) | (Original Assignee) Telefonaktiebolaget LM Ericsson AB
(Current Assignee)
Telefonaktiebolaget LM Ericsson AB
| Method, and associated apparatus, for selectively permitting access by a mobile terminal to a packet data network | ▪ wireless communication ≈ wireless communication
▪ original data ≈ coupled thereto
▪ step b, step d ≈ including a, comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b)
▪ 35 U.S.C. 102(e) | ▪ teaches allowing users of a TV device to formulate queries and developing user profiles based upon these queries the…
▪ teaches a timeout limit during an authentication procedure…
▪ teaches wherein the meta data comprises application data for being usable in an application executable on the…
▪ discloses the above limitations but does not disclose a method as described in claim… | X | | | | | X | | X | X | | | | | | | | | | |
108
 | US6078269A
(Scott Markwell, 2000) | (Original Assignee) Safenight Tech Inc
(Current Assignee)
Google LLC
| Battery-powered, RF-interconnected detector sensor system | ▪ wireless communication network ≈ signal transmission
▪ wireless network technology ≈ transmitted data
▪ transmitting unit ≈ receiving means, emitting diode
▪ intrusion detection module ≈ motion sensor
▪ time interval ≈ time interval
▪ step b, step d ≈ including a, comprises a
▪ first receiving ≈ data check
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b) | ▪ discloses that logging the send alarms allows for the ability to verify that the alarms were properly sent and received…
▪ discloses several participants are assembled in a group and a group membership is contained in the list see…
▪ discloses a detector sensor system where a detector can be a motion detector and signals from one detector can be…
▪ teaches sensor readings are of environmental conditions selected from a group consisting of temperature humidity… | X | X | | | X | | | | X | X | X | | X | X | X | X | X | X | X |
109
 | US6115376A
(W. Paul Sherer, 2000) | (Original Assignee) 3Com Corp
(Current Assignee)
HP Inc
;
Hewlett Packard Enterprise Development LP
| Medium access control address authentication | ▪ wireless communication network ≈ non-volatile memory
▪ step b, step d ≈ including a
▪ incoming data, incoming data frames ≈ other port
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ teaches a system relating to security in the data networks and authentication of sources of data carrying a medium…
▪ discloses an authentication method for network access comprising…
▪ teaches that it is desirable that the algorithm of a frame body part in the MAC frame that is transmitted and received…
▪ teaches the monitoring unit comprises a table of correspondence specifying for each port connected to the connection… | X | | | | | | X | X | X | X | | X | | | | X | X | | |
110
 | US6298250B1
(Byard G. Nilsson, 2001) | (Original Assignee) BETTINA JEAN THOMPSON; KUYPER REENA (ONE-EIGHTH INTEREST)
(Current Assignee)
Dot 23 Technologies LLC
| Wireless prepaid telephone system with extended capability | ▪ wireless communication ≈ wireless communication
▪ step b, step d ≈ including a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ teaches wherein marketing information is audibly transmitted to the user over the network col…
▪ teaches a housing wherein the member includes a support for locating and retaining a printed circuit board thereon see…
▪ teaches a housing including a guide on the body to receive and support electronic components mounted on the member see…
▪ discloses the use of a text communication account the combination of HAMILTON and NILSSON does not expressly disclose… | X | | | | | | | | X | | | | | | | | | | |
111
 | US6154775A
(Michael John Coss, 2000) | (Original Assignee) Nokia of America Corp
(Current Assignee)
Palo Alto Networks Inc
| Methods and apparatus for a computer network firewall with dynamic rule processing with the ability to dynamically alter the operations of rules | ▪ second receiving unit ≈ comprises information
▪ step d ≈ comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b)
▪ 35 U.S.C. 102(e) | ▪ discloses a networked personal contact manager title comprising address books for multiple users where users can link to…
▪ teaches displaying an email address as a unique string col…
▪ teaches to set readwritedelete permissions for reserved user space in the wireless module data store…
▪ teaches storing information regarding a user s contacts ie acquaintances and allows users to search each other s… | | | | | | | | | | X | | | | | | | X | | |
112
 | US6222856B1
(Murali R. Krishnan, 2001) | (Original Assignee) Microsoft Corp
(Current Assignee)
Microsoft Technology Licensing LLC
| Adaptive bandwidth throttling for individual virtual services supported on a network server | ▪ original data frames, data frames ≈ predetermined bandwidth, receiving requests
▪ step a, step b ≈ following steps
▪ step d ≈ time intervals
▪ incoming data frames, data processing unit ≈ fixed time
▪ air interface ≈ apply one
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses a system wherein the feed personalization module is further configured to evaluate whether service of the feed…
▪ teaches a computerimplemented method comprising receiving through a network interface of a computer system coupled to…
▪ teaches keeping bandwidth utilized within a threshold of B plus or minus a delta…
▪ discloses that a network server is an ISP that provides services to a client over the… | X | | X | X | X | X | X | X | X | X | | | | | | X | X | | |
113
 | US5958053A
(John Stewart Denker, 1999) | (Original Assignee) AT&T Corp
(Current Assignee)
AT&T Corp
| Communications protocol with improved security | ▪ outgoing data ≈ established connection
▪ step a, step b ≈ following steps, including a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b)
▪ 35 U.S.C. 102(e) | ▪ discloses an invention wherein the implementation of a protocol that embeds packets is made sensitive to the type of…
▪ discloses a method for determining a presence status of a user comprising obtaining…
▪ teaches and describes a system and method that relates to a system and method which provides connectivity between one…
▪ teaches load balancing of the plurality of virtual servers further comprises enabling at least one geographic based… | | | X | X | X | | | | | | | | | | | X | X | | |
114
 | US5852351A
(Ronald G. Canada, 1998) | (Original Assignee) CSI Technology Inc
(Current Assignee)
Computational Systems Inc
| Machine monitor | ▪ original data ≈ store information
▪ transmission channels ≈ clock signals
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b) | ▪ teaches wherein said processor is programmed to calculate the second value of the operating condition of the component…
▪ teaches a controller obtains an analysis result on a status of the motor using…
▪ teaches wherein the first value is one of an average a rolling average a mode a median a range and a standard…
▪ teaches a device for monitoring a machine that remotely alarms a user that a problem has occurred with the machine… | X | | | | | X | | X | X | X | | | | | | | X | | |
115
 | US5919257A
(Jonathan Trostle, 1999) | (Original Assignee) Micro Focus Software Inc
(Current Assignee)
RPX Corp
| Networked workstation intrusion detection system | ▪ outgoing data frames, outgoing data frames comprises frames ≈ station identifier
▪ first receiving, first receiving unit ≈ algorithm t
▪ step d ≈ comprises a, said method
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b)
▪ 35 U.S.C. 102(e) | ▪ discloses this step to allow software and data to be transferred between computer system…
▪ discloses that the BIOS upgrade is validated by using a digital signature that is embedded in the BIOS upgrade…
▪ discloses the creation of hash values for hashes for each of a plurality of database objects programs at a server see…
▪ teaches if the integrity fails a trusted repository is accessed to obtain a valid replacement component… | | | X | X | X | | | | | X | | | | | | X | X | | |
116
 | US6016318A
(Hiroyuki Tomoike, 2000) | (Original Assignee) NEC Corp
(Current Assignee)
NEC Corp
| Virtual private network system over public mobile data network and virtual LAN | ▪ incoming data, incoming traffic ≈ information signal
▪ data processing unit ≈ processing units
▪ step b, step d ≈ including a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses a virtual private network system over a public mobile data network and…
▪ discloses separate sets of queues are associated with separate guest operating systems executing on the host computer…
▪ teaches a wireless station comprising A wireless transceiver at least one network interface connected to the radio…
▪ teaches a reception system featuring the use of supplemental data for the purpose of improving reception performance… | X | | | | | | X | X | X | X | | | | | | X | X | | |
117
 | JPH1117806A
(Susumu Matsui, 1999) | (Original Assignee) Hitachi Ltd; 株式会社日立製作所 | Information reception processing method and computer / telephony integration system | ▪ outgoing data ≈ registration process
▪ original data frames ≈ 記憶手段と
▪ air interface ≈ said contact
▪ incoming data, incoming traffic ≈ sender side
▪ step b, step d ≈ includes a
▪ impersonation detection system, data processing unit ≈ apparatus
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b)
▪ 35 U.S.C. 102(e) | ▪ teaches transferring emails from a user home account to a wireless device…
▪ teaches wherein the lowlevel descriptor language is extensible markup language XML column…
▪ teaches sending information via the wireless local area network information representative of a internet web page user…
▪ discloses that many SIP response codes are identical to the corresponding HTTP… | X | | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X |
118
 | WO9826548A1
(Jim Y. Li, 1998) | (Original Assignee) Whistle Communications Corporation | Automatic configuration for internet access device | ▪ wireless network ≈ Internet service provider
▪ step a, step b ≈ following steps, including a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ teaches the invention substantially as claims discussed above…
▪ teaches a faxdata modem device that enables a computer system to make FAX or data call via a single telephone line…
▪ teaches having plurality of software software objects and hardware systems of managing and monitoring the IP network…
▪ teaches an apparatus comprising a a receiverclient s browser configured to receive information the information… | | | | | | | | | | | | | | | X | X | | | X |
119
 | US6028537A
(Michael J. Suman, 2000) | (Original Assignee) Prince Corp USA
(Current Assignee)
Visteon Global Technologies Inc
| Vehicle communication and remote control system | ▪ second receiving, second receiving unit ≈ phone calls
▪ step b, step d ≈ including a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b)
▪ 35 U.S.C. 102(e) | ▪ teaches a system wherein the means for determining the location are incorporated into the device GPS module…
▪ teaches wherein the transmission device is operable to transmit the control signals at least twice col…
▪ discloses a method comprising accessing a location of the device the location determined from pseudo ranges between the…
▪ teaches detecting vehicle abnormal situation door being ajar prioritizing the abnormal condition via response center… | | | | | | | | | | X | | | | | | | X | | |
120
 | US6173399B1
(Sidney A. Gilbrech, 2001) | (Original Assignee) VPNet Technologies Inc
(Current Assignee)
Avaya Inc
;
VPNet Technologies Inc
| Apparatus for implementing virtual private networks | ▪ communication protocol ≈ Internet Protocol
▪ step d ≈ comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b)
▪ 35 U.S.C. 102(e) | ▪ discloses a method for providing customized advertisement to mobile users based on their profile US…
▪ teaches of hosts on a LAN comprising by the relay device detecting the private IP address and a MAC address of the…
▪ discloses architecture for virtual private network including the following features…
▪ teaches of a virtual network environment wherein the server notifies the relay device of the virtual network IP… | | | | | | | | | | | | X | | | | | | | |
121
 | US6021495A
(Vipin Kumar Jain, 2000) | (Original Assignee) 3Com Corp
(Current Assignee)
HP Inc
;
Hewlett Packard Enterprise Development LP
| Method and apparatus for authentication process of a star or hub network connection ports by detecting interruption in link beat | ▪ wireless node ≈ network nodes
▪ incoming data, incoming data frames ≈ other port
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses wherein the digital rights information is a pointer to link a user to a property rights database…
▪ teaches that timestamps can be used as a substitute to random in authentication to prevent replay attacks…
▪ teaches a second access point receiving a handoff request in paragraph…
▪ discloses an authentication method for authenticating a mobile station in which the mobile node sends its subscriber… | X | X | | | | | X | X | X | X | | X | X | X | | X | X | | |
122
 | EP0814393A1
(Anders Eriksson, 1997) | (Original Assignee) Telia AB
(Current Assignee)
Telia AB
| Control and supervision of electrical components | ▪ impersonation detection signal ≈ measurement result
▪ wireless communication network ≈ managing unit
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b)
▪ 35 U.S.C. 102(e) | ▪ teaches users actions may be monitored in order to provide better service to the users of the system wherein the…
▪ teaches wherein each control option is associated with a sequence of commands that when executed sends instructions to…
▪ teaches a monitoring system that monitors food for spoilage…
▪ teaches the transducer access device responds to search requests from the control pointcontrol device searching for… | X | | | | | | | | X | X | | | | | | | | | |
123
 | US5907491A
(Ronald G. Canada, 1999) | (Original Assignee) CSI Technology Inc
(Current Assignee)
Computational Systems Inc
| Wireless machine monitoring and communication system | ▪ incoming data ≈ receiving wireless signals
▪ time interval ≈ predetermined time period
▪ step b, step d ≈ first predetermined time, including a
▪ wireless communication ≈ wireless communication
▪ communication protocol ≈ transferring data
▪ intrusion attack ≈ designated time
▪ step a ≈ said machine
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b) | ▪ teaches a wireless machine monitoring and communication system including means for monitoring vibration signals and…
▪ discloses all the limitations of the base claims as outlined above…
▪ discloses a system comprising the following features vehicle…
▪ teaches selectively entering a sleep mode to reduce power consumption see… | X | | | | X | | X | X | X | X | X | X | | | | X | X | X | |
124
 | EP0793170A1
(Graham Hamilton, 1997) | (Original Assignee) Sun Microsystems Inc
(Current Assignee)
Sun Microsystems Inc
| System and method for automatic configuration of home network computers | ▪ data frames ≈ receiving requests
▪ step b, step d ≈ including a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b)
▪ 35 U.S.C. 102(e) | ▪ discloses a system and method for automatic con guration of home network computers that combines and stores the local…
▪ teaches that electronic devices such as computers have col…
▪ discloses all subject matter of the claimed invention as discussed above with respect to claim…
▪ teaches having plurality of software software objects and hardware systems of managing and monitoring the IP network… | X | | X | X | X | X | X | X | X | X | | | | | | X | X | | |
125
 | US5931946A
(Masato Terada, 1999) | (Original Assignee) Hitachi Ltd
(Current Assignee)
Hitachi Ltd
| Network system having external/internal audit system for computer security | ▪ time interval ≈ predetermined time period
▪ second receiving unit ≈ repeating units
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b) | ▪ teaches wherein the network information includes a list of wireless access point devices and associated parameters…
▪ discloses the spam determination at then may include comparing the determined or calculated score andor confidence level…
▪ discloses a computerized method of monitoring for a user a denial of service attack upon a target network resource see…
▪ teaches a of different attack scenarios which a single source of attack directs its attack toward either a single… | | | | | X | | | | | X | | | | | | | X | | |
126
 | US5913041A
(Srinivas Ramanathan, 1999) | (Original Assignee) HP Inc
(Current Assignee)
Viavi Solutions Inc
| System for determining data transfer rates in accordance with log information relates to history of data transfer activities that independently stored in content servers | ▪ data frames ≈ receiving requests
▪ communication protocol ≈ Internet Protocol, transferring data
▪ step b, step d ≈ including a, comprises a
▪ outgoing data, outgoing data frames ≈ n channels
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses a providing service control device according to claim…
▪ teaches the tracking of data transfers within a network system…
▪ discloses an email system that provides the ability to re assemble objects at a replication site such that an object and…
▪ discloses that intranet internet protocol address is assigned to the first user from a plurality of intranet internet… | X | | X | X | X | X | X | X | X | X | | X | | | | X | X | | |
127
 | US5796942A
(Daniel Esbensen, 1998) | (Original Assignee) CA Inc
(Current Assignee)
CA Inc
| Method and apparatus for automated network-wide surveillance and security breach intervention | ▪ original data ≈ reading data
▪ incoming traffic ≈ data packet
| | | X | | | | | X | | X | X | X | | | | | | | X | | |
128
 | US5898830A
(Ralph E. Wesinger, 1999) | (Original Assignee) Network Engr Software
(Current Assignee)
GraphOn Corp
| Firewall providing enhanced network security and user transparency | ▪ first receiving ≈ computer instructions
▪ intrusion attack ≈ first firewall
▪ communication protocol ≈ first packet
▪ incoming traffic ≈ data packet
▪ step d ≈ comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b)
▪ 35 U.S.C. 102(e) | ▪ discloses the secure network wherein all data transmitted from one network device to another network device traverses…
▪ teaches encrypting encoding key data transmission delivering information other than publicity available program and…
▪ teaches if user desire contract to have advertising inserted for subscription current actual cost per unit time is…
▪ teaches the invention substantially as claimed including application program and documentation generator system and… | | | | | | | | | | X | X | X | | | | | X | X | |
129
 | US5892903A
(Christopher W. Klaus, 1999) | (Original Assignee) Internet Security Systems Inc
(Current Assignee)
International Business Machines Corp
| Method and apparatus for detecting and identifying security vulnerabilities in an open network computer communication system | ▪ intrusion attack ≈ network communications
▪ second receiving unit, second receiving ≈ predetermined value, source addresses
▪ communication protocol ≈ Internet Protocol
▪ original data ≈ coupled thereto
▪ step d ≈ step d
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b) | ▪ teaches methods for risk rating and detecting malicious online ads see…
▪ teaches wherein the network information includes a list of wireless access point devices and associated parameters…
▪ discloses the spam determination at then may include comparing the determined or calculated score andor confidence level…
▪ teaches a of different attack scenarios which a single source of attack directs its attack toward either a single… | X | | | | | X | | X | X | X | X | X | | | | | X | X | |
130
 | US5854994A
(Ronald G. Canada, 1998) | (Original Assignee) CSI Technology Inc
(Current Assignee)
Computational Systems Inc
| Vibration monitor and transmission system | ▪ incoming data, incoming traffic ≈ receiving wireless signals, power consumption
▪ communication protocol ≈ communication protocol, transferring data
▪ transmission channels ≈ frequency domain, clock signals
▪ data frames ≈ time period
▪ step d ≈ comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b) | ▪ teaches a wireless machine monitoring and communication system including means for monitoring vibration signals and…
▪ discloses all the limitations of the base claims as outlined above…
▪ discloses a system comprising the following features vehicle…
▪ teaches selectively entering a sleep mode to reduce power consumption see… | X | | X | X | X | X | X | X | X | X | | X | | | | X | X | | |
131
 | US5726911A
(Ronald G. Canada, 1998) | (Original Assignee) CSI Technology Inc
(Current Assignee)
Computational Systems Inc
| Electric motor monitor | ▪ time interval ≈ predetermined time period
▪ transmission channels ≈ temperature ranges
▪ step d ≈ comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b) | ▪ teaches wherein said processor is programmed to calculate the second value of the operating condition of the component…
▪ teaches a controller obtains an analysis result on a status of the motor using…
▪ teaches wherein the first value is one of an average a rolling average a mode a median a range and a standard…
▪ teaches a device for monitoring a machine that remotely alarms a user that a problem has occurred with the machine… | | | | | X | | | | | X | | | | | | | X | | |
132
 | US5870610A
(William J. Beyda, 1999) | (Original Assignee) Siemens Business Communication Systems Inc
(Current Assignee)
Enterprise Systems Technologies SARL
| Autoconfigurable method and system having automated downloading | ▪ wireless node ≈ transmission lines
▪ intrusion attack ≈ said devices
▪ step d ≈ said method
| | | X | X | | | | | X | | X | X | X | | X | X | | X | X | X | |
133
 | US6009363A
(Richard D. Beckert, 1999) | (Original Assignee) Microsoft Corp
(Current Assignee)
Microsoft Technology Licensing LLC
| Vehicle computer system with high speed data buffer and serial interconnect | ▪ data processing unit ≈ processing units
▪ incoming traffic ≈ master clock
▪ step b ≈ clock pulses
▪ step d ≈ comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses wherein the first portion of the electronic system includes an audio transmission circuit…
▪ discloses the seizing of a second channel in the case of failure of a first channel…
▪ teaches that the decrypting the digest associated with the software component using a public key column…
▪ discloses a display panel with a plurality of connections to external input devices see… | | | | | | | | | | X | | | | | | | X | | |
134
 | WO9631077A1
(Dalibor Turina, 1996) | (Original Assignee) Telefonaktiebolaget Lm Ericsson (Publ) | Method and arrangement in a radio communication system | ▪ step a, step b ≈ following steps
▪ incoming data, incoming traffic ≈ time slots
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ discloses a system comprising a data interface eg transmission system…
▪ teaches the known technique the predetermined threshold level comprises a predetermined period of time has lapsed…
▪ discloses separate sets of queues are associated with separate guest operating systems executing on the host computer…
▪ teaches that priority value can be received and stored in USIM card… | X | | | | | | X | X | X | X | | | | | | X | X | | |
135
 | US5793476A
(Peter Laakmann, 1998) | (Original Assignee) Lidatek LLC
(Current Assignee)
CHL REVOCABLE TRUST
| Laser transponder and method for disabling laser speed monitors | ▪ time interval ≈ predetermined time period, selected time period
▪ second receiving ≈ carrier frequency
▪ first receiving ≈ transmitting step
▪ step b, step d ≈ including a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b) | ▪ teaches that for manned aircraft collisions with ground and air based obstacles results in numerous fatalities each…
▪ discloses combining the fused image with symbols representing objects…
▪ teaches a photodiode for the light detector that generates a detection signal for transmission to a signal processor…
▪ teaches an array of object detection beams for detecting objects in the front monitored area and the rear monitored… | | | | | X | | | | | X | | | | | | | X | | |
136
 | US5794164A
(Richard D. Beckert, 1998) | (Original Assignee) Microsoft Corp
(Current Assignee)
Microsoft Technology Licensing LLC
| Vehicle computer system | ▪ wireless communication ≈ wireless communication
▪ transmitting unit, transmitting outgoing data frames ≈ receiving device
▪ data processing unit ≈ processing units
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses wherein the first portion of the electronic system includes an audio transmission circuit…
▪ discloses the seizing of a second channel in the case of failure of a first channel…
▪ teaches that the decrypting the digest associated with the software component using a public key column…
▪ discloses a display panel with a plurality of connections to external input devices see… | X | | | | | | | | X | X | | | X | | | X | X | | |
137
 | US20010040885A1
(Howard Jonas, 2001) | (Original Assignee) International Discount Telecommunications Corp; Net2phone Inc
(Current Assignee)
International Discount Telecommunications Corp
;
Net2phone Inc
| Method and apparatus for transmitting and routing voice telephone calls over a packet switched computer network | ▪ time interval, data processing unit ≈ packet format
▪ step b, step d ≈ including a, comprises a
▪ incoming traffic ≈ data packet
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e)
▪ 35 U.S.C. 102(b) | ▪ discloses that the charge to a user in a packet switched network is based on the amount of information transmitted see…
▪ teaches a connection and packet level multiplexing between network links…
▪ teaches wherein a received data packet of the plurality of received data packets is formatted based on a different…
▪ discloses a method and system for establishing a telephone call between the computer and telephone device via internet… | | | | | X | | | | | X | | | | | | | X | | |
138
 | US5659195A
(William J. Kaiser, 1997) | (Original Assignee) University of California
(Current Assignee)
University of California
| CMOS integrated microsensor with a precision measurement circuit | ▪ original data, data processing unit ≈ first semiconductor
▪ step b, step d ≈ including a, comprises a
▪ air interface ≈ top layer
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b) | ▪ discloses wherein said thermal actuators are electromagnetic actuator wherein said thermal actuators provide actuation…
▪ teaches an insulating member ZR between the adjacent capacitance electrodes being the same as the insulating base…
▪ teaches depositing of a polysilicon but lacks depositing a seed layer and then epitaxially depositing epipoly thereon…
▪ teaches it is the preferred material for the base and with the column and walls of… | X | | | | | X | | X | X | X | | | | | | X | X | | |
139
 | JPH08186569A
(Junko Ami, 1996) | (Original Assignee) Toshiba Corp; 株式会社東芝 | Address management device and address management method | ▪ original data frames ≈ 記憶手段と
▪ transmitting unit ≈ receiving means
▪ wireless node ≈ ノード間
▪ impersonation detection system, data processing unit ≈ apparatus, detecting
| | | X | X | | | | X | X | X | X | X | X | X | X | X | X | X | X | X | X |
140
 | US5745759A
(Patrick M. Hayden, 1998) | (Original Assignee) QNX Software Systems Ltd
(Current Assignee)
2236008 Ontario Inc
;
8758271 Canada Inc
| Window kernel | ▪ step a, step b ≈ following steps, including a
▪ second receiving, second receiving unit ≈ second planar, first area
▪ first receiving ≈ device signal
▪ first receiving unit ≈ said area
| | | | | | | | | | | | X | | | | | | | X | | |
141
 | US5553076A
(Saman Behtash, 1996) | (Original Assignee) TCSI Corp
(Current Assignee)
Atmel Corp
| Method and apparatus for a wireless local area network | ▪ wireless communication ≈ wireless communication
▪ first receiving ≈ transmitting step
▪ transmitting unit ≈ receiving means
▪ step d ≈ said method
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ discloses wherein a first communication transmission is from the first backhaul access point to the first repeater…
▪ teaches the known technique the predetermined threshold level comprises a predetermined period of time has lapsed…
▪ discloses separate sets of queues are associated with separate guest operating systems executing on the host computer…
▪ teaches the step of authorizing stations prior to granting the allocation… | X | | | | | | | | X | X | | | X | | | | X | | |
142
 | US5557742A
(Stephen E. Smaha, 1996) | (Original Assignee) Haystack Labs Inc
(Current Assignee)
McAfee LLC
| Method and system for detecting intrusion into and misuse of a data processing system | ▪ original data ≈ object information
▪ step d ≈ comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ discloses user authentication is typically implemented in the form of password protection for a system…
▪ teaches a security monitoring apparatus based on access log wherein representation of the time of the most recent read…
▪ discloses excessive storage user but not excessive system service use…
▪ discloses software product comprising instructions stored on computer readable media wherein the instructions when… | X | | | | | X | | X | X | | | | | | | | | | |
143
 | WO9417606A1
(Michael A. Fischer, 1994) | (Original Assignee) Digital Ocean, Inc. | Medium access control protocol for wireless network | ▪ step a ≈ spreading code
▪ data frames, incoming data frames ≈ second frame, one frame
▪ step b, step d ≈ including a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b) | ▪ discloses a method wherein speci c information is provided to a device…
▪ discloses turning on communicators for transmitting and receiving data and turning off the communicator when they are…
▪ teaches that each remote communicator must repeatedly measure the time from receipt of the information frame until the…
▪ teaches a medium access control MAC technique or protocol for selectively activating and deactivating the transmitters… | X | | X | X | X | X | X | X | X | X | | | | | | X | X | | |
144
 | JPH07154859A
(Kenichi Ishida, 1995) | (Original Assignee) Mitsubishi Electric Corp; 三菱電機株式会社 | Mobile equipment, switching center, and mobile communication system | ▪ step a ≈ selection control
▪ original data, original data frames ≈ シーケンス
▪ impersonation detection signal ≈ 上記移動機
▪ step b, step d ≈ includes a
▪ second receiving, second receiving unit ≈ reception
| | | X | | | | | X | | X | X | X | | | | | | | X | | |
145
 | US5424808A
(Kazunobu Maekawa, 1995) | (Original Assignee) Minolta Co Ltd
(Current Assignee)
Minolta Co Ltd
| Control apparatus for copying machine with improved communication function for centralized control unit | ▪ second receiving unit ≈ predetermined value
▪ transmitting unit ≈ receiving means
▪ step d, step b ≈ comprises a, including a
▪ original data, original data frames ≈ paper jam
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b) | ▪ discloses a memory for registering an electronic mail address and wherein in a case where an electronic mail is received…
▪ discloses wherein information indicating a printing apparatus may comprise a printer model or a unique name…
▪ teaches a method of examining the threshold value and alerting the user and vendor of consumables that are in need of…
▪ teaches a data processing apparatus connected to a printing apparatus… | X | | | | | X | | X | X | X | | | X | | | | X | | |
146
 | US5428636A
(Robert C. Meier, 1995) | (Original Assignee) Norand Corp
(Current Assignee)
Avago Technologies General IP Singapore Pte Ltd
;
Innovatio IP Ventures LLC
| Radio frequency local area network | ▪ wireless communication ≈ present location
▪ step a ≈ node b
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b)
▪ 35 U.S.C. 102(e) | ▪ discloses having a node remain awake for the minimal time necessary to receive the next HELLO packet the intent is not…
▪ teaches a method for implementing a short range wireless communication system see…
▪ discloses a power consumption reducing apparatus comprising a periodic active state conversion unit which in each awake…
▪ discloses the wireless sensor system where in the system and method of… | X | | | | | | | | X | | | | | | | | | | |
147
 | US5760530A
(Edward S. Kolesar, 1998) | (Original Assignee) US Air Force
(Current Assignee)
US Air Force
| Piezoelectric tactile sensor | ▪ intrusion detection module, intrusion detection module incoming data frames ≈ determining presence
▪ transmitting unit ≈ area portion
▪ step b, step d ≈ including a, step b
| ▪ 35 U.S.C. 103(a) | ▪ teaches two piezoelectric elements on each end of the touch sensor but does not teach a second displacement section is… | X | X | | | | | | | X | X | X | | X | X | | X | X | X | |
148
 | US5287110A
(My Tran, 1994) | (Original Assignee) Honeywell Inc
(Current Assignee)
Honeywell Inc
| Complementary threat sensor data fusion method and apparatus | ▪ data processing unit ≈ solving means
▪ second receiving unit ≈ elapsed time
▪ step b, step d ≈ including a, comprises a
| ▪ 35 U.S.C. 103(a) | ▪ discloses the method pertaining to matrix operations wherein an average value is calculated along the diagonal of a…
▪ discloses that components that have bers dependent on optical path length and input wavelengths can be used as…
▪ teaches a method of estimating an arcposition of a distal transmitter… | | | | | | | | | | X | | | | | | | X | | |
149
 | JPH0661903A
(Kazuhisa Tsubaki, 1994) | (Original Assignee) Matsushita Electric Ind Co Ltd; 松下電器産業株式会社 | Intercom | ▪ impersonation detection system, data processing unit ≈ apparatus
▪ second receiving, second receiving unit ≈ reception
▪ transmitting original data frames, transmitting outgoing data frames ≈ 符復号
| | | X | | | | | | | | X | X | X | X | X | X | X | X | X | X | X |
150
 | US5241542A
(Kadathur S. Natarajan, 1993) | (Original Assignee) International Business Machines Corp
(Current Assignee)
Lenovo Singapore Pte Ltd
| Battery efficient operation of scheduled access protocol | ▪ wireless communication ≈ wireless communication
▪ impersonation detection system ≈ remaining time
▪ data frames, incoming data frames ≈ second frame, time slots
▪ step b, step d ≈ including a, said method
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b) | ▪ discloses sending a null data frame to the current access point with a power save bit turned on…
▪ discloses disabling power save poll generation in the client…
▪ discloses during scheduling AP indicating to STA to transmit frame and frame utilizes…
▪ discloses a system and method for sharing bandwidth by a plurality of devices in a wireless personal area network or… | X | | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X |
151
 | US5247564A
(Robert G. Zicker, 1993) | (Original Assignee) GTE Mobile Communications Service Corp
(Current Assignee)
GTE Wireless Inc
| Adaptive vehicle alarm detection and reporting system | ▪ transmitting outgoing data frames ≈ mobile radio
▪ second receiving, second receiving unit ≈ phone calls
▪ step d ≈ comprises a, said method
▪ step a ≈ step a
▪ step b ≈ step b
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b)
▪ 35 U.S.C. 102(e) | ▪ teaches mounting a radio receiving unit in a trunk lid or shaped adaptation for accumulating the radio receiver unit…
▪ discloses a control system and method for a vehicle in which signals for activating deactivating enabling and disabling…
▪ teaches the maintenance menu comprises an item to modify input delete or save at least one of a sales volume of a…
▪ discloses an analogous art vehicle tracking and security system with position determining that comprises an… | | | | | | | | | | X | | | | | | X | X | | |
152
 | US4855713A
(Robert E. Brunius, 1989) | (Original Assignee) Interactive Technologies Inc
(Current Assignee)
Carrier Fire and Security Americas Corp
| Learn mode transmitter | ▪ time interval ≈ temporarily store
▪ step d ≈ comprises a
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(e) | ▪ discloses the routing information base is implemented as a link state database that stores the sensor information…
▪ discloses several participants are assembled in a group and a group membership is contained in the list see…
▪ teaches a surveillance network comprising a controller a plurality of sensors being capable of communicating with the…
▪ discloses transmitted to an intended recipient participant by way of one or more intermediating participants and further… | | | | | X | | | | | | | | | | | | | | |
153
 | US4951029A
(Paul K. Severson, 1990) | (Original Assignee) Interactive Technologies Inc
(Current Assignee)
Carrier Fire and Security Americas Corp
| Micro-programmable security system | ▪ air interface ≈ first system controller, communication link
▪ original data ≈ coupled thereto
▪ second receiving ≈ first reporting
▪ communication protocol ≈ control signals
▪ transmitting unit ≈ receiving means
▪ step b, step d ≈ including a, comprises a
| | | X | | | | | X | | X | X | X | | X | X | | | X | X | | |
154
 | US4876545A
(Christopher M. Carlson, 1989) | (Original Assignee) ITT Corp
(Current Assignee)
ITT Inc
| Adaptive blanking interface apparatus for self-protection jamming equipment employed in conjunction with radar systems | ▪ step d, step b ≈ change information, including a
▪ time interval ≈ real time basis
▪ transmitting unit ≈ receiving means
| ▪ 35 U.S.C. 103(a)
▪ 35 U.S.C. 102(b) | ▪ discloses the method pertaining to matrix operations wherein an average value is calculated along the diagonal of a…
▪ teaches wherein the communications jamming systems communicate with one another via radiofrequency links wherein the…
▪ teaches the sensor system is configured to monitor a space which is a ship and the sensor data is transmitted to a…
▪ discloses an upconverter for shifting the frequency of the transmitted signal… | | | | | X | | | | | | | | X | | | | | | |
155
 | US4812820A
(Ian M. Chatwin, 1989) | (Original Assignee) Chatwin Ian Malcolm | Electronic surveillance system and transceiver unit therefor | ▪ incoming data ≈ logic circuitry
▪ incoming traffic ≈ other units
| | | X | | | | | | X | X | X | X | | | | | | X | X | | |
156
 | US4520674A
(Ronald G. Canada, 1985) | (Original Assignee) Technology for Energy Corp
(Current Assignee)
TECHNOLOGY FOR ENERGY Corp A CORP
;
Technology for Energy Corp
;
Fifth Third Bank NA
| Vibration monitoring device | ▪ step a ≈ power supply means, said machine
▪ incoming data, incoming traffic ≈ power consumption
▪ wireless node, wireless communication ≈ including analog
▪ transmission channels ≈ frequency domain
▪ step d ≈ comprises a
| | | X | X | | | | | X | X | X | X | | | X | X | | X | X | | |
US7409715B2
Filed: 2003-12-10 Issued: 2008-08-05
Mechanism for detection of attacks based on impersonation in a wireless network
(Original Assignee) Alcatel Lucent SAS (Current Assignee)
Wsou Investments LLC
Frederic Gariador, Vinod Kumar Choyi, Andrew Robison | US6208247B1
Filed: 1998-08-18 Issued: 2001-03-27
Wireless integrated sensor network using multiple relayed communications
(Original Assignee) Rockwell Science Center LLC (Current Assignee)
Skyworks Solutions Inc
Jonathan R. Agre, Loren P. Clare, 5th Henry O. Marcy, Allen J. Twarowski, William Kaiser, Wilmer A. Mickelson, Michael D. Yakos, Christian J. Loeffelholz, Jonathan R. Engdahl |
|---|
US7409715B2
CLAIM 1 . A method for detecting impersonation based attacks at a wireless node of a wireless communication network , comprising the steps of : a) operatively connecting the wireless node with an intrusion detection module and providing the intrusion detection module with a copy of original data frames (second station, data buffer, time period, n channels) transmitted by the wireless node over a wireless interface ;
b) detecting at the intrusion detection module incoming data frames received over the wireless interface ;
c) comparing at the intrusion detection module the information in the copy with the information in the incoming data frames ;
and d) recognizing an impersonating attack when the intrusion detection module determines that the information in the copy differs from the information in the incoming data frames . |
US6208247B1
CLAIM 1 . An electronic communicating and sensing station , comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor , to transmit information about the sensed condition , and a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
wherein said transmitter and receiver operate in a plurality of communication channels (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) that are defined time period (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) s , subdivisions of a longer periodically repeating time frame .
US6208247B1
CLAIM 3 . An electronic communicating and sensing station , comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor , to transmit information about the sensed condition , a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
a data buffer (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) for storing data from said sensor , a spectral analyzer which operates on the data in said data buffer , to compute a power spectral density in at least one spectral band , and one or more comparators , each comparing the power spectral density in a respective spectral band computed by said spectral analyzer with a respective stored power spectral density and producing an output signal when said power spectral density exceeds said stored power spectral density , the output signals from said comparators together forming the output of said digital signal processor .
US6208247B1
CLAIM 9 . A network of electronic communicating and sensing stations , comprising at least two stations , a first station and a second station (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) , each comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor to transmit information about the sensed condition , and a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
wherein said second station is arranged to communicate with said first station by receiving said information by said wireless receiver ;
and wherein said digital signal processor comprises : a data buffer for storing data from said sensor , a spectrum analyzer which operates on the data in said dati buffer , to compute a power spectral density in at least on(spectral band , and one or more comparators , each comparing the power spectral density in a respective spectral band computed by said spectrum analyzer with a respective stored power spectral density and producing an output signal when said power spectral density exceeds said stored power spectral density , the outputs from said comparators together forming the output of said digital signal processor .
|
US7409715B2
CLAIM 4 . The method of claim 1 , wherein the copy includes a summary of the outgoing data frames (second station, data buffer, time period, n channels) . |
US6208247B1
CLAIM 1 . An electronic communicating and sensing station , comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor , to transmit information about the sensed condition , and a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
wherein said transmitter and receiver operate in a plurality of communication channels (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) that are defined time period (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) s , subdivisions of a longer periodically repeating time frame .
US6208247B1
CLAIM 3 . An electronic communicating and sensing station , comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor , to transmit information about the sensed condition , a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
a data buffer (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) for storing data from said sensor , a spectral analyzer which operates on the data in said data buffer , to compute a power spectral density in at least one spectral band , and one or more comparators , each comparing the power spectral density in a respective spectral band computed by said spectral analyzer with a respective stored power spectral density and producing an output signal when said power spectral density exceeds said stored power spectral density , the output signals from said comparators together forming the output of said digital signal processor .
US6208247B1
CLAIM 9 . A network of electronic communicating and sensing stations , comprising at least two stations , a first station and a second station (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) , each comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor to transmit information about the sensed condition , and a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
wherein said second station is arranged to communicate with said first station by receiving said information by said wireless receiver ;
and wherein said digital signal processor comprises : a data buffer for storing data from said sensor , a spectrum analyzer which operates on the data in said dati buffer , to compute a power spectral density in at least on(spectral band , and one or more comparators , each comparing the power spectral density in a respective spectral band computed by said spectrum analyzer with a respective stored power spectral density and producing an output signal when said power spectral density exceeds said stored power spectral density , the outputs from said comparators together forming the output of said digital signal processor .
|
US7409715B2
CLAIM 5 . The method of claim 4 , wherein the summary of the outgoing data frames (second station, data buffer, time period, n channels) comprises frames that allow statistical comparisons . |
US6208247B1
CLAIM 1 . An electronic communicating and sensing station , comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor , to transmit information about the sensed condition , and a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
wherein said transmitter and receiver operate in a plurality of communication channels (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) that are defined time period (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) s , subdivisions of a longer periodically repeating time frame .
US6208247B1
CLAIM 3 . An electronic communicating and sensing station , comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor , to transmit information about the sensed condition , a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
a data buffer (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) for storing data from said sensor , a spectral analyzer which operates on the data in said data buffer , to compute a power spectral density in at least one spectral band , and one or more comparators , each comparing the power spectral density in a respective spectral band computed by said spectral analyzer with a respective stored power spectral density and producing an output signal when said power spectral density exceeds said stored power spectral density , the output signals from said comparators together forming the output of said digital signal processor .
US6208247B1
CLAIM 9 . A network of electronic communicating and sensing stations , comprising at least two stations , a first station (first receiving, first receiving unit, second receiving unit, outgoing data frames comprises frames) and a second station (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) , each comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor to transmit information about the sensed condition , and a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
wherein said second station is arranged to communicate with said first station by receiving said information by said wireless receiver ;
and wherein said digital signal processor comprises : a data buffer for storing data from said sensor , a spectrum analyzer which operates on the data in said dati buffer , to compute a power spectral density in at least on(spectral band , and one or more comparators , each comparing the power spectral density in a respective spectral band computed by said spectrum analyzer with a respective stored power spectral density and producing an output signal when said power spectral density exceeds said stored power spectral density , the outputs from said comparators together forming the output of said digital signal processor .
|
US7409715B2
CLAIM 6 . The method of claim 4 , wherein the summary comprises the number of the outgoing data frames (second station, data buffer, time period, n channels) transmitted over a time interval (time interval) . |
US6208247B1
CLAIM 1 . An electronic communicating and sensing station , comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor , to transmit information about the sensed condition , and a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
wherein said transmitter and receiver operate in a plurality of communication channels (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) that are defined time period (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) s , subdivisions of a longer periodically repeating time frame .
US6208247B1
CLAIM 3 . An electronic communicating and sensing station , comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor , to transmit information about the sensed condition , a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
a data buffer (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) for storing data from said sensor , a spectral analyzer which operates on the data in said data buffer , to compute a power spectral density in at least one spectral band , and one or more comparators , each comparing the power spectral density in a respective spectral band computed by said spectral analyzer with a respective stored power spectral density and producing an output signal when said power spectral density exceeds said stored power spectral density , the output signals from said comparators together forming the output of said digital signal processor .
US6208247B1
CLAIM 6 . The station of claim 5 , further comprising : a sum-of-squares accumulator , which operates on the filtered data output of said digital filter , squares the filtered data output from said digital filters and accumulates the squared filtered data output over a time interval (time interval) to obtain an average power spectral density for application as an input to said comparators .
US6208247B1
CLAIM 9 . A network of electronic communicating and sensing stations , comprising at least two stations , a first station and a second station (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) , each comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor to transmit information about the sensed condition , and a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
wherein said second station is arranged to communicate with said first station by receiving said information by said wireless receiver ;
and wherein said digital signal processor comprises : a data buffer for storing data from said sensor , a spectrum analyzer which operates on the data in said dati buffer , to compute a power spectral density in at least on(spectral band , and one or more comparators , each comparing the power spectral density in a respective spectral band computed by said spectrum analyzer with a respective stored power spectral density and producing an output signal when said power spectral density exceeds said stored power spectral density , the outputs from said comparators together forming the output of said digital signal processor .
|
US7409715B2
CLAIM 7 . The method of claim 4 , wherein the summary comprises the types of the original data frames (second station, data buffer, time period, n channels) . |
US6208247B1
CLAIM 1 . An electronic communicating and sensing station , comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor , to transmit information about the sensed condition , and a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
wherein said transmitter and receiver operate in a plurality of communication channels (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) that are defined time period (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) s , subdivisions of a longer periodically repeating time frame .
US6208247B1
CLAIM 3 . An electronic communicating and sensing station , comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor , to transmit information about the sensed condition , a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
a data buffer (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) for storing data from said sensor , a spectral analyzer which operates on the data in said data buffer , to compute a power spectral density in at least one spectral band , and one or more comparators , each comparing the power spectral density in a respective spectral band computed by said spectral analyzer with a respective stored power spectral density and producing an output signal when said power spectral density exceeds said stored power spectral density , the output signals from said comparators together forming the output of said digital signal processor .
US6208247B1
CLAIM 9 . A network of electronic communicating and sensing stations , comprising at least two stations , a first station and a second station (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) , each comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor to transmit information about the sensed condition , and a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
wherein said second station is arranged to communicate with said first station by receiving said information by said wireless receiver ;
and wherein said digital signal processor comprises : a data buffer for storing data from said sensor , a spectrum analyzer which operates on the data in said dati buffer , to compute a power spectral density in at least on(spectral band , and one or more comparators , each comparing the power spectral density in a respective spectral band computed by said spectrum analyzer with a respective stored power spectral density and producing an output signal when said power spectral density exceeds said stored power spectral density , the outputs from said comparators together forming the output of said digital signal processor .
|
US7409715B2
CLAIM 8 . The method of claim 1 , wherein step b) comprises monitoring all wireless channels allocated to the wireless node and extracting the incoming data frames (second station, data buffer, time period, n channels) received over all the wireless channels allocated to the wireless node . |
US6208247B1
CLAIM 1 . An electronic communicating and sensing station , comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor , to transmit information about the sensed condition , and a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
wherein said transmitter and receiver operate in a plurality of communication channels (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) that are defined time period (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) s , subdivisions of a longer periodically repeating time frame .
US6208247B1
CLAIM 3 . An electronic communicating and sensing station , comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor , to transmit information about the sensed condition , a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
a data buffer (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) for storing data from said sensor , a spectral analyzer which operates on the data in said data buffer , to compute a power spectral density in at least one spectral band , and one or more comparators , each comparing the power spectral density in a respective spectral band computed by said spectral analyzer with a respective stored power spectral density and producing an output signal when said power spectral density exceeds said stored power spectral density , the output signals from said comparators together forming the output of said digital signal processor .
US6208247B1
CLAIM 9 . A network of electronic communicating and sensing stations , comprising at least two stations , a first station and a second station (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) , each comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor to transmit information about the sensed condition , and a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
wherein said second station is arranged to communicate with said first station by receiving said information by said wireless receiver ;
and wherein said digital signal processor comprises : a data buffer for storing data from said sensor , a spectrum analyzer which operates on the data in said dati buffer , to compute a power spectral density in at least on(spectral band , and one or more comparators , each comparing the power spectral density in a respective spectral band computed by said spectrum analyzer with a respective stored power spectral density and producing an output signal when said power spectral density exceeds said stored power spectral density , the outputs from said comparators together forming the output of said digital signal processor .
|
US7409715B2
CLAIM 9 . The method of claim 1 , wherein step d) comprises : correlating the original data frames (second station, data buffer, time period, n channels) with the incoming data frames for detecting an inconsistency between the frames ;
and upon detection of the inconsistency , further processing the incoming data frames for qualifying the impersonating attack . |
US6208247B1
CLAIM 1 . An electronic communicating and sensing station , comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor , to transmit information about the sensed condition , and a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
wherein said transmitter and receiver operate in a plurality of communication channels (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) that are defined time period (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) s , subdivisions of a longer periodically repeating time frame .
US6208247B1
CLAIM 3 . An electronic communicating and sensing station , comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor , to transmit information about the sensed condition , a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
a data buffer (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) for storing data from said sensor , a spectral analyzer which operates on the data in said data buffer , to compute a power spectral density in at least one spectral band , and one or more comparators , each comparing the power spectral density in a respective spectral band computed by said spectral analyzer with a respective stored power spectral density and producing an output signal when said power spectral density exceeds said stored power spectral density , the output signals from said comparators together forming the output of said digital signal processor .
US6208247B1
CLAIM 9 . A network of electronic communicating and sensing stations , comprising at least two stations , a first station and a second station (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) , each comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor to transmit information about the sensed condition , and a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
wherein said second station is arranged to communicate with said first station by receiving said information by said wireless receiver ;
and wherein said digital signal processor comprises : a data buffer for storing data from said sensor , a spectrum analyzer which operates on the data in said dati buffer , to compute a power spectral density in at least on(spectral band , and one or more comparators , each comparing the power spectral density in a respective spectral band computed by said spectrum analyzer with a respective stored power spectral density and producing an output signal when said power spectral density exceeds said stored power spectral density , the outputs from said comparators together forming the output of said digital signal processor .
|
US7409715B2
CLAIM 10 . An impersonation detection system for a wireless node of a wireless communication network , the node for transmitting original data frames (second station, data buffer, time period, n channels) over a wireless interface comprising : an intrusion detection module for correlating the original data frames with incoming data frames received over the air interface ;
and connection means between the wireless node and the intrusion detection module for providing the intrusion detection module with a copy of the original data frames . |
US6208247B1
CLAIM 1 . An electronic communicating and sensing station , comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor , to transmit information about the sensed condition , and a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
wherein said transmitter and receiver operate in a plurality of communication channels (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) that are defined time period (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) s , subdivisions of a longer periodically repeating time frame .
US6208247B1
CLAIM 3 . An electronic communicating and sensing station , comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor , to transmit information about the sensed condition , a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
a data buffer (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) for storing data from said sensor , a spectral analyzer which operates on the data in said data buffer , to compute a power spectral density in at least one spectral band , and one or more comparators , each comparing the power spectral density in a respective spectral band computed by said spectral analyzer with a respective stored power spectral density and producing an output signal when said power spectral density exceeds said stored power spectral density , the output signals from said comparators together forming the output of said digital signal processor .
US6208247B1
CLAIM 9 . A network of electronic communicating and sensing stations , comprising at least two stations , a first station and a second station (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) , each comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor to transmit information about the sensed condition , and a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
wherein said second station is arranged to communicate with said first station by receiving said information by said wireless receiver ;
and wherein said digital signal processor comprises : a data buffer for storing data from said sensor , a spectrum analyzer which operates on the data in said dati buffer , to compute a power spectral density in at least on(spectral band , and one or more comparators , each comparing the power spectral density in a respective spectral band computed by said spectrum analyzer with a respective stored power spectral density and producing an output signal when said power spectral density exceeds said stored power spectral density , the outputs from said comparators together forming the output of said digital signal processor .
|
US7409715B2
CLAIM 11 . The impersonation detection system of claim 10 , wherein the intrusion detection module comprises : a first receiving (first station) unit for receiving the copy ;
an antenna for capturing the incoming traffic received on all transmission channels allocated to the wireless node ;
a second receiving unit (first station) for detecting the incoming data frames (second station, data buffer, time period, n channels) from the incoming traffic ;
and a data processing unit (second station, data buffer, time period, n channels) for correlating the copy with the incoming data frames and generating a impersonation detection signal . |
US6208247B1
CLAIM 1 . An electronic communicating and sensing station , comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor , to transmit information about the sensed condition , and a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
wherein said transmitter and receiver operate in a plurality of communication channels (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) that are defined time period (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) s , subdivisions of a longer periodically repeating time frame .
US6208247B1
CLAIM 3 . An electronic communicating and sensing station , comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor , to transmit information about the sensed condition , a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
a data buffer (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) for storing data from said sensor , a spectral analyzer which operates on the data in said data buffer , to compute a power spectral density in at least one spectral band , and one or more comparators , each comparing the power spectral density in a respective spectral band computed by said spectral analyzer with a respective stored power spectral density and producing an output signal when said power spectral density exceeds said stored power spectral density , the output signals from said comparators together forming the output of said digital signal processor .
US6208247B1
CLAIM 9 . A network of electronic communicating and sensing stations , comprising at least two stations , a first station (first receiving, first receiving unit, second receiving unit, outgoing data frames comprises frames) and a second station (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) , each comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor to transmit information about the sensed condition , and a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
wherein said second station is arranged to communicate with said first station by receiving said information by said wireless receiver ;
and wherein said digital signal processor comprises : a data buffer for storing data from said sensor , a spectrum analyzer which operates on the data in said dati buffer , to compute a power spectral density in at least on(spectral band , and one or more comparators , each comparing the power spectral density in a respective spectral band computed by said spectrum analyzer with a respective stored power spectral density and producing an output signal when said power spectral density exceeds said stored power spectral density , the outputs from said comparators together forming the output of said digital signal processor .
|
US7409715B2
CLAIM 17 . A wireless node for a wireless network comprising : means for transmitting outgoing data frames (second station, data buffer, time period, n channels) over a wireless interface ;
an intrusion detection module for correlating the outgoing data frames with incoming data frames received from the air interface ;
and a secure link between the wireless node and the intrusion detection module for providing the intrusion detection module with a copy of the outgoing data frames . |
US6208247B1
CLAIM 1 . An electronic communicating and sensing station , comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor , to transmit information about the sensed condition , and a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
wherein said transmitter and receiver operate in a plurality of communication channels (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) that are defined time period (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) s , subdivisions of a longer periodically repeating time frame .
US6208247B1
CLAIM 3 . An electronic communicating and sensing station , comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor , to transmit information about the sensed condition , a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
a data buffer (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) for storing data from said sensor , a spectral analyzer which operates on the data in said data buffer , to compute a power spectral density in at least one spectral band , and one or more comparators , each comparing the power spectral density in a respective spectral band computed by said spectral analyzer with a respective stored power spectral density and producing an output signal when said power spectral density exceeds said stored power spectral density , the output signals from said comparators together forming the output of said digital signal processor .
US6208247B1
CLAIM 9 . A network of electronic communicating and sensing stations , comprising at least two stations , a first station and a second station (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) , each comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor to transmit information about the sensed condition , and a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
wherein said second station is arranged to communicate with said first station by receiving said information by said wireless receiver ;
and wherein said digital signal processor comprises : a data buffer for storing data from said sensor , a spectrum analyzer which operates on the data in said dati buffer , to compute a power spectral density in at least on(spectral band , and one or more comparators , each comparing the power spectral density in a respective spectral band computed by said spectrum analyzer with a respective stored power spectral density and producing an output signal when said power spectral density exceeds said stored power spectral density , the outputs from said comparators together forming the output of said digital signal processor .
|
US7409715B2
CLAIM 18 . The wireless node of claim 17 , wherein the intrusion detection module comprises : a first receiving (first station) unit for receiving the copy of the outgoing data frames (second station, data buffer, time period, n channels) ;
an antenna for capturing the incoming traffic carried on all transmission channels allocated to the wireless node ;
a second receiving unit (first station) for detecting the incoming data frames from the incoming traffic ;
and a data processing unit (second station, data buffer, time period, n channels) for correlating the copy of the outgoing data frames with the incoming data frames and generating an impersonation detected signal . |
US6208247B1
CLAIM 1 . An electronic communicating and sensing station , comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor , to transmit information about the sensed condition , and a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
wherein said transmitter and receiver operate in a plurality of communication channels (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) that are defined time period (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) s , subdivisions of a longer periodically repeating time frame .
US6208247B1
CLAIM 3 . An electronic communicating and sensing station , comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor , to transmit information about the sensed condition , a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
a data buffer (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) for storing data from said sensor , a spectral analyzer which operates on the data in said data buffer , to compute a power spectral density in at least one spectral band , and one or more comparators , each comparing the power spectral density in a respective spectral band computed by said spectral analyzer with a respective stored power spectral density and producing an output signal when said power spectral density exceeds said stored power spectral density , the output signals from said comparators together forming the output of said digital signal processor .
US6208247B1
CLAIM 9 . A network of electronic communicating and sensing stations , comprising at least two stations , a first station (first receiving, first receiving unit, second receiving unit, outgoing data frames comprises frames) and a second station (data frames, original data frames, incoming data frames, outgoing data frames, data processing unit, transmitting original data frames, outgoing data) , each comprising : a sensor which provides an output indicative of a sensed condition , a digital signal processor , coupled to receive the sensor output and configured to compare characteristics of the sensor output to a stored set of characteristics , and producing an output based upon said comparison , a programmable microprocessor coupled to said digital signal processor to evaluate its output , a wireless transmitter that is controlled by said programmable microprocessor to transmit information about the sensed condition , and a wireless receiver that is controlled by said programmable microprocessor to receive data and instructions for programming said programmable microprocessor ;
wherein said second station is arranged to communicate with said first station by receiving said information by said wireless receiver ;
and wherein said digital signal processor comprises : a data buffer for storing data from said sensor , a spectrum analyzer which operates on the data in said dati buffer , to compute a power spectral density in at least on(spectral band , and one or more comparators , each comparing the power spectral density in a respective spectral band computed by said spectrum analyzer with a respective stored power spectral density and producing an output signal when said power spectral density exceeds said stored power spectral density , the outputs from said comparators together forming the output of said digital signal processor .
|





























































































































































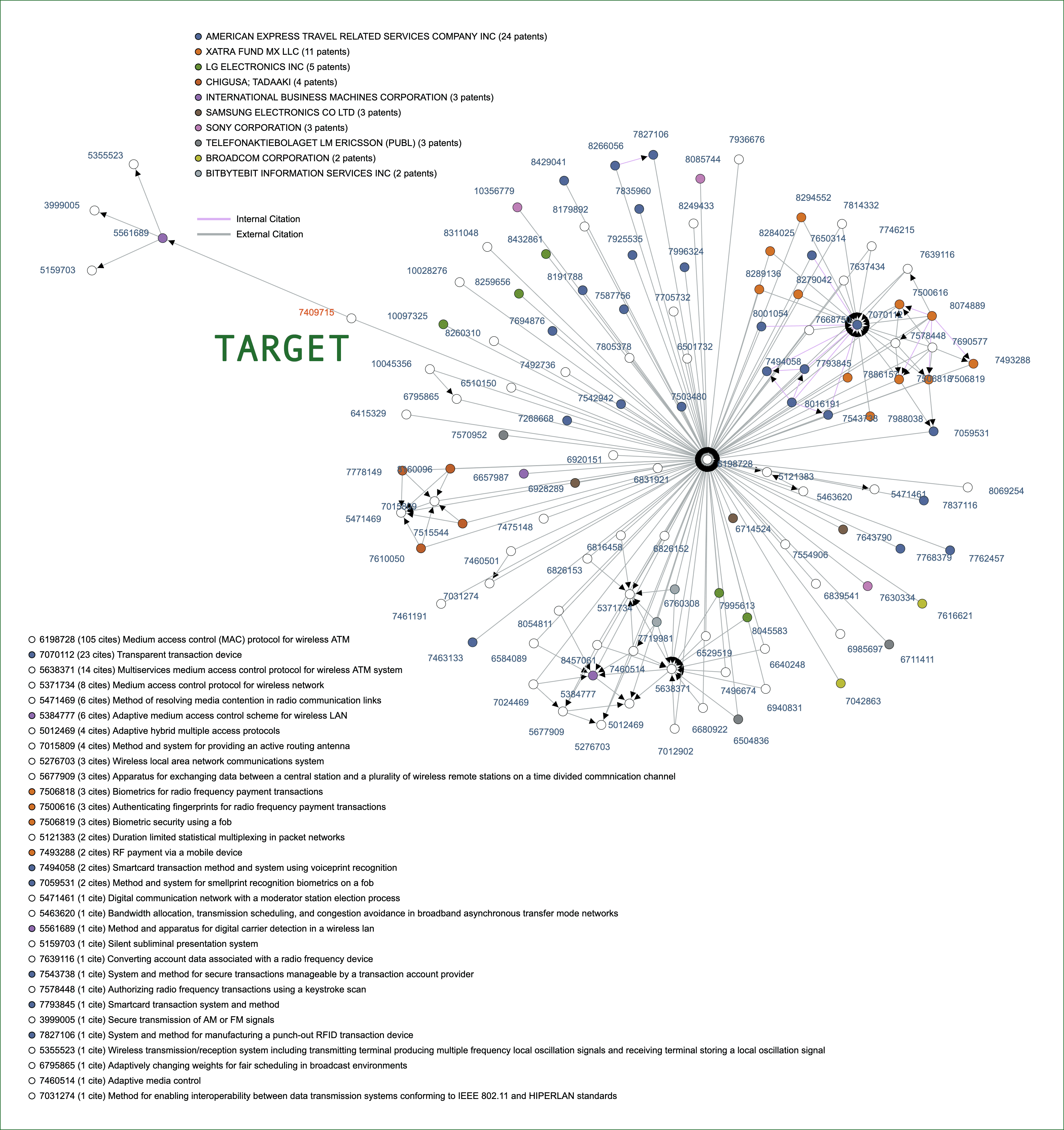
 KR Prior Art
KR Prior Art